OffSec Module: Malware Detection using Machine Learning
Co-authored by Iftekharul Haque (Hawk) Here, we first choose what kind of machine learning model we want to use in this process. As anyone with some little machine learning model
Co-authored by Iftekharul Haque (Hawk) Here, we first choose what kind of machine learning model we want to use in this process. As anyone with some little machine learning model
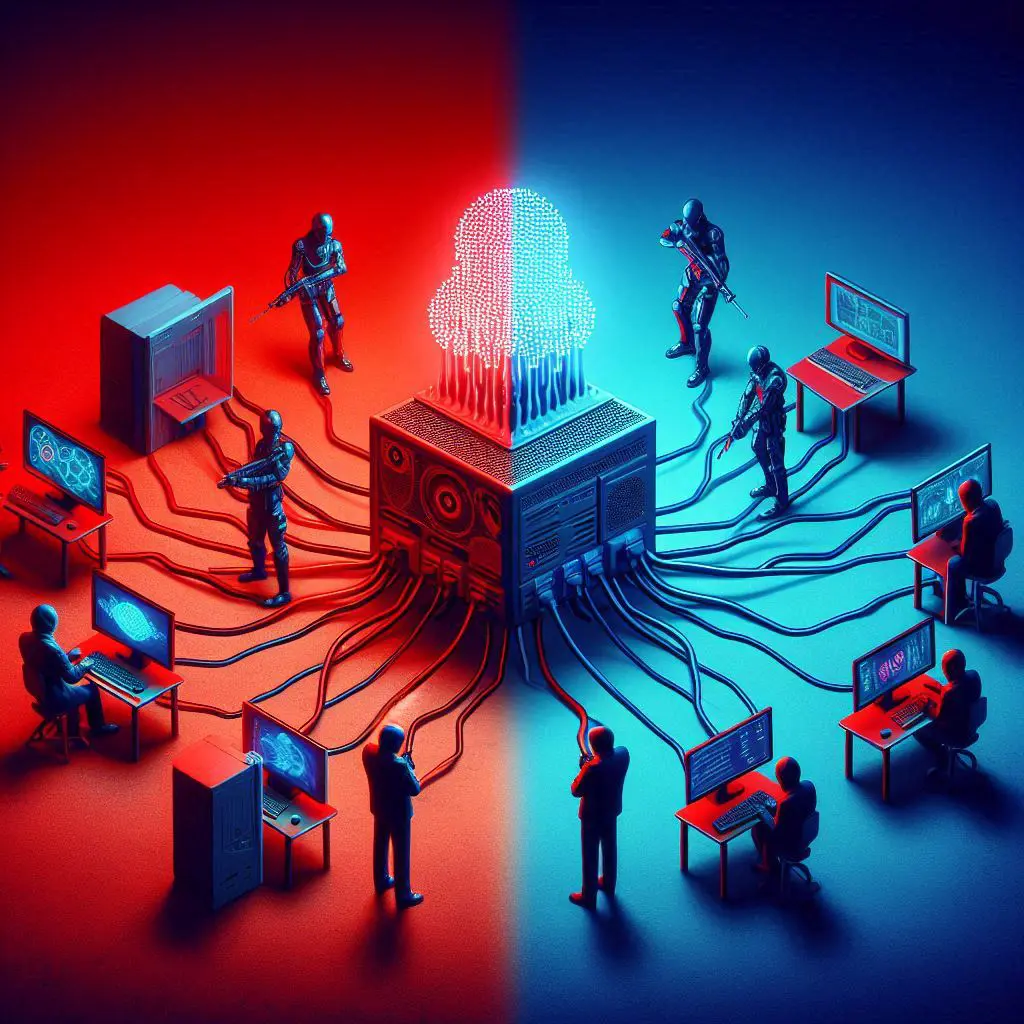
In today’s world, our workstations, servers, and mobile devices are more vulnerable than ever. They are prime targets for cybercriminals looking to execute malicious code and infiltrate networks. With

In this write-up, we will explore how to effectively hunt for ransomware from a network perspective, focusing on identifying Indicators of Compromise (IoCs) related to LockBit ransomware. The scenario in

As I continue my journey through the OffSec TH-200 course, I’ve now reached Module 2, Section 1, which delves into some critical areas of cybersecurity: threat actors, ransomware groups,
