QRadar Security Breach Analysis
Security Incident Summary
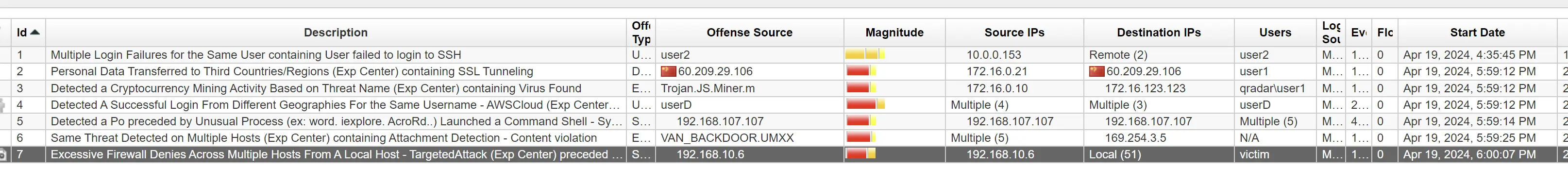
On April 19, 2024, between 4:35 PM and 6:00 PM, our network experienced a coordinated cyberattack involving multiple offenses. The incident began with over 109 million failed SSH login attempts targeting a Linux server. Following this, attackers managed to install a backdoor malware via phishing emails, which allowed them to gain persistence on multiple hosts. Subsequently, unauthorized AWS EC2 instances were created, and cryptocurrency mining malware was detected on the network. The attackers then conducted local scans, including database scans, and used FTP to download data from critical servers. Finally, data exfiltration to an IP address in China was identified, suggesting the culmination of their efforts to extract sensitive information. Despite the firewall blocking some traffic, it was unable to prevent all unauthorized downloads and data transfers.
Offense 1
Time of incident: Apr 19, 2024, 4:35:45 PM
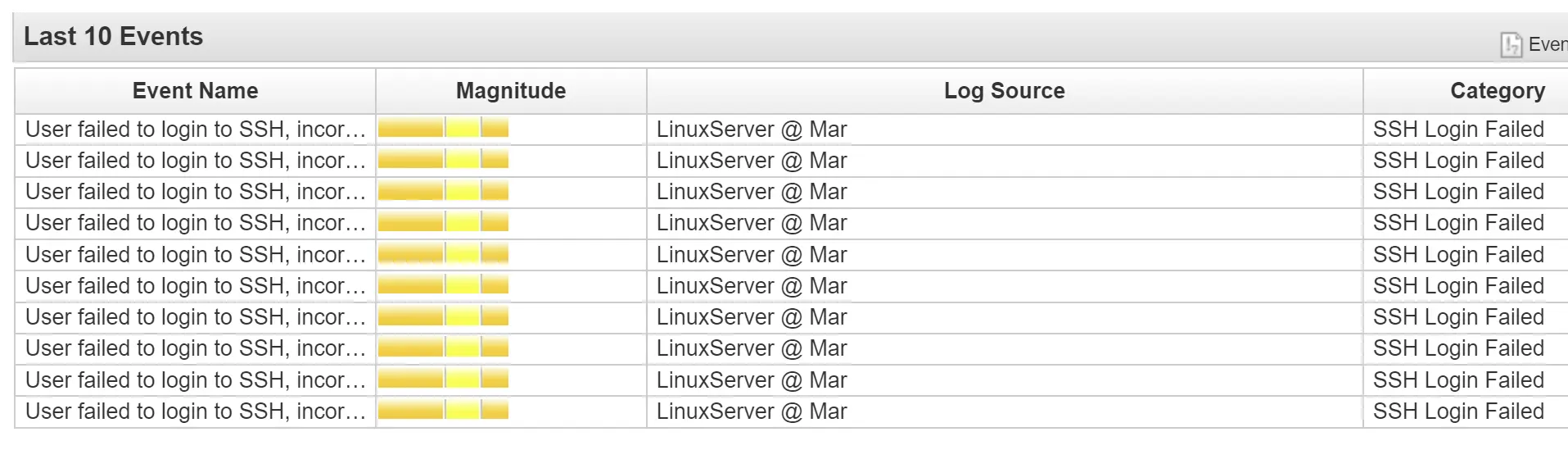
Multiple Login Failures for the Same User containing User failed to login to SSH
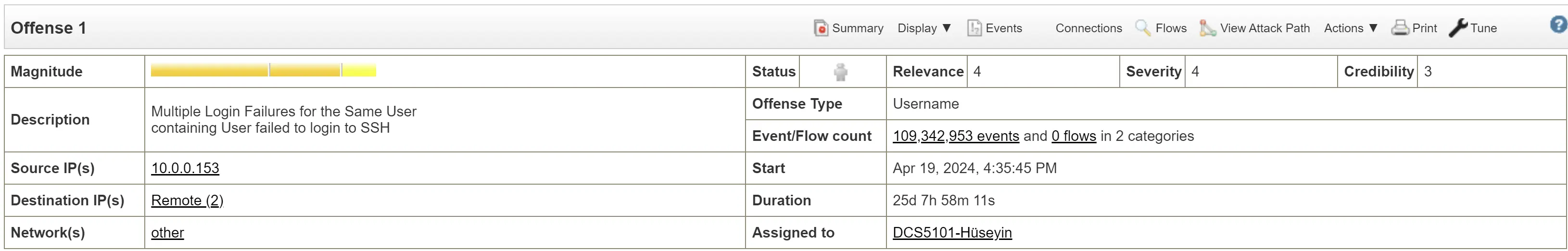
Targeted user: user2
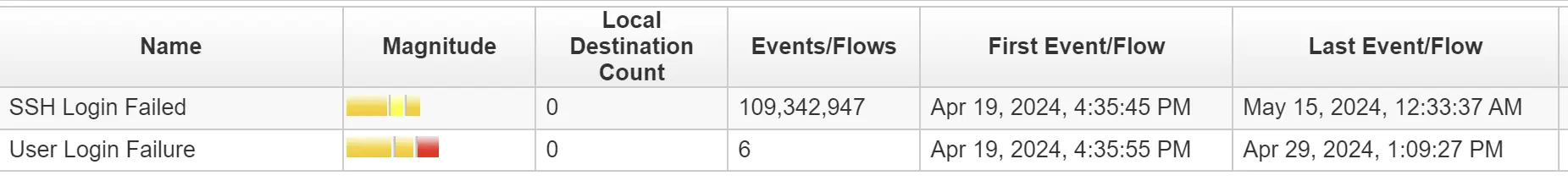
Attempts First started on April 19th 2024 and have been going on until May 15th 2024
Over 109 million failed attempts for ssh (remote) and 6 failed user attempts.
Attempts to log into a linux server
[10] "Destination/Event Analysis". The number of events this source generated during this attack, was deemed worth a value of 10 on a scale of 0-10, with higher values indicating high volumes of events generated, and lower numbers indicating a smaller grade attack.
Of the 109,342,947 failed sign in attempts, the IP's that participated in the attack include but are not limited to:
- 10.0.0.153 (212,104 attempts for a single rule trigger)
Mitigation Strategy
Blacklist 10.0.0.153
Offense 2
Time of incident: Apr 19, 2024, 5:59:12 PM
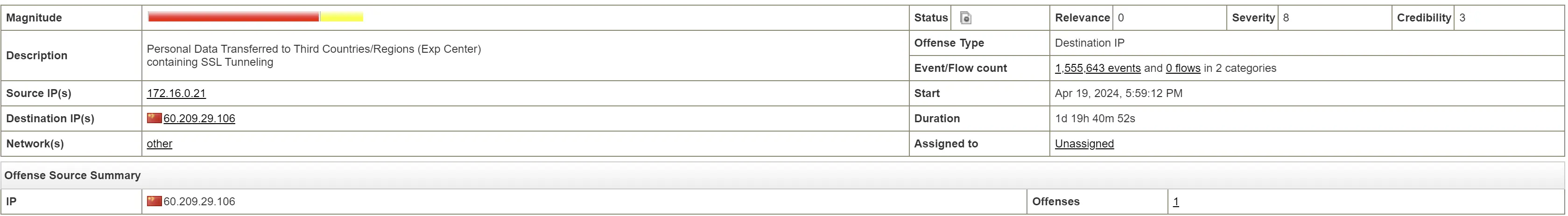
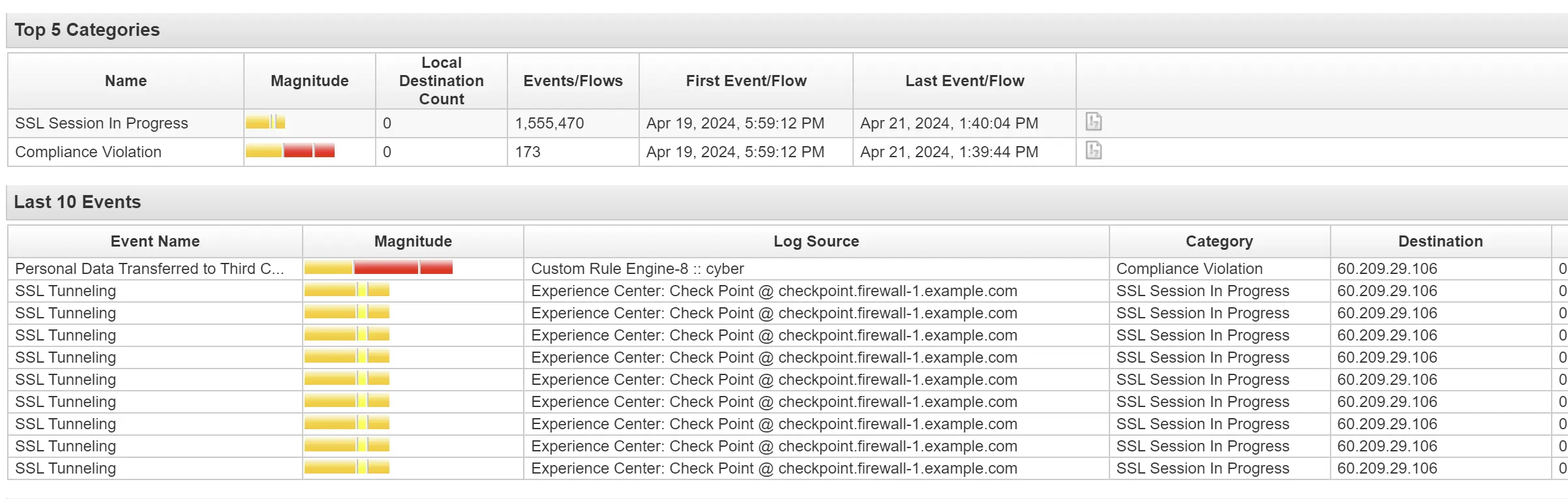
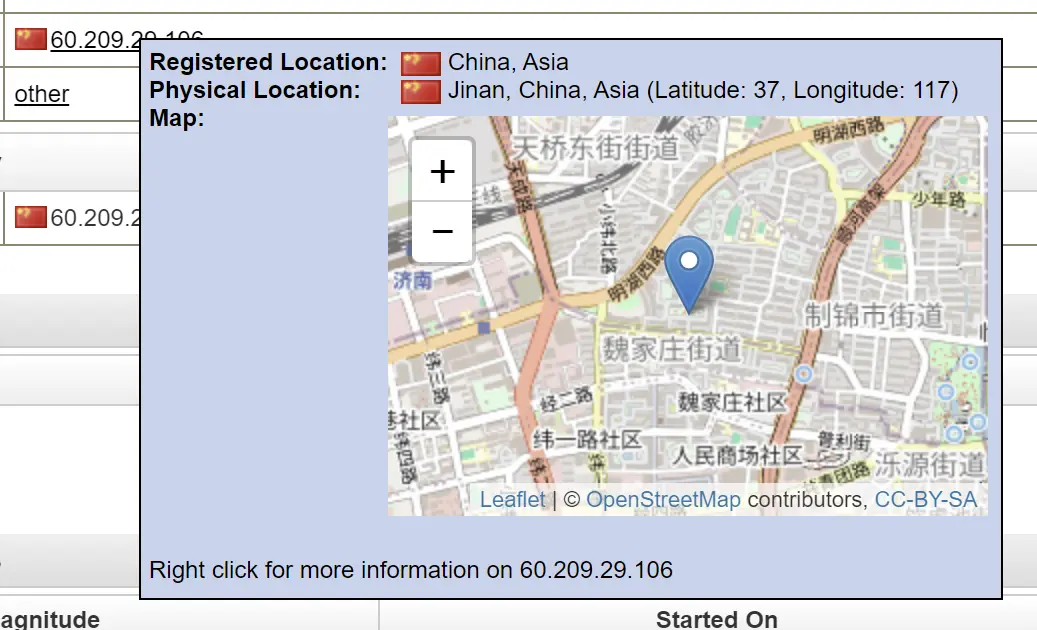
Attack IP: 60.209.29.106
Located in China
Rules
"CRE Event". CRE Rule description: [Personal Data Transferred to Third Countries/Regions (Exp Center)] Personal data are detected being transferred to Third Countries/Regions. Note that these countries/regions are defined in ECBB:CategoryDefinition: Destination IP is a Third Country/Region. Edit this Experience Center BB according to your business use case.