PicoCTF - trickster

This is a challenge from picoCTF titled 'trickster' from web exploitation category. It's needless to say that this one is a little trickier as the name suggests but the concept is really cool.
You can access the challenge here.
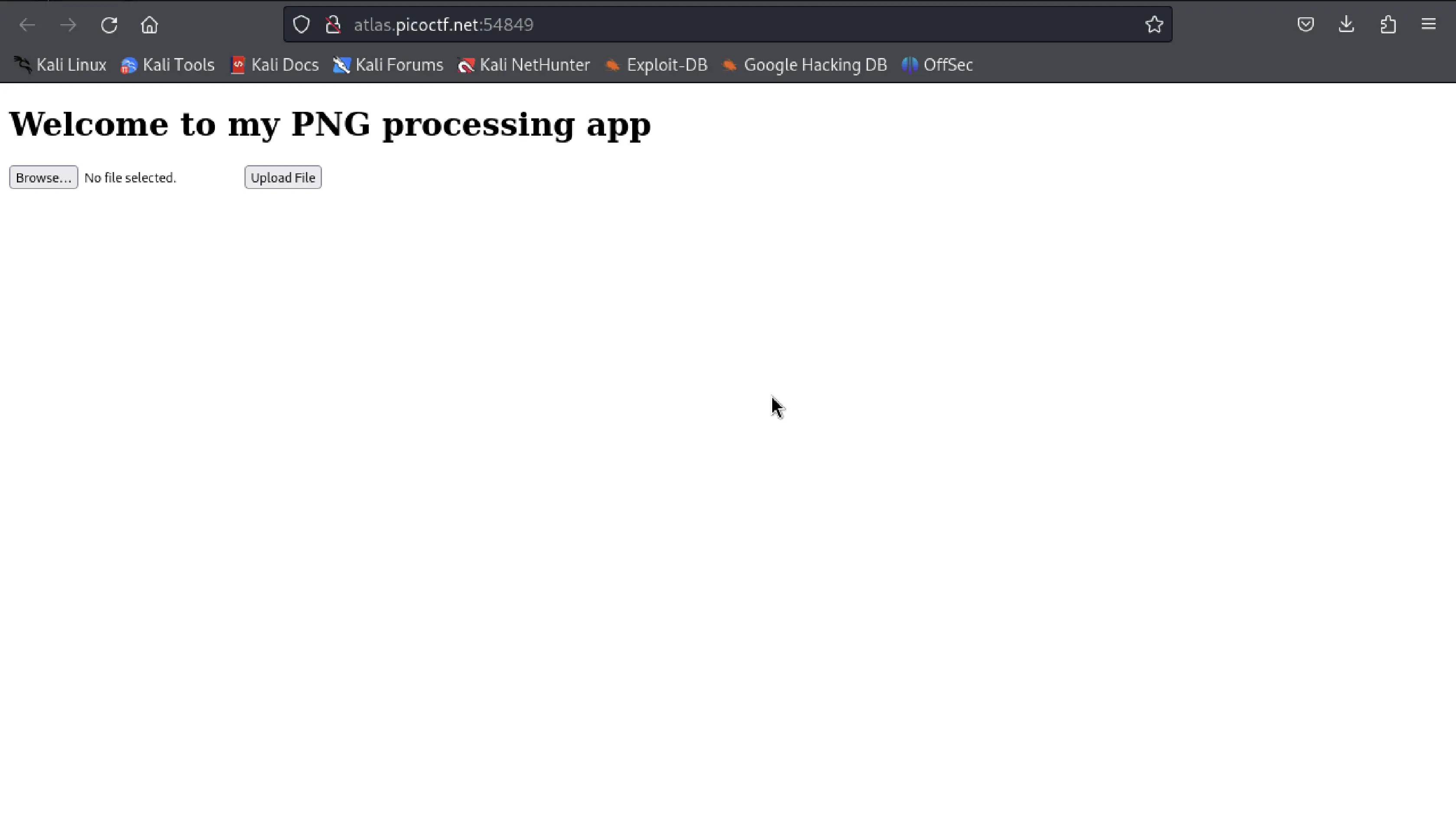
Upon launching the instance, it redirects me to a website called File Upload Page. From initial recon, I understood that the page has an upload functionality where the user can only upload image of .png extension. The website doesn't allow submitting any other file type.
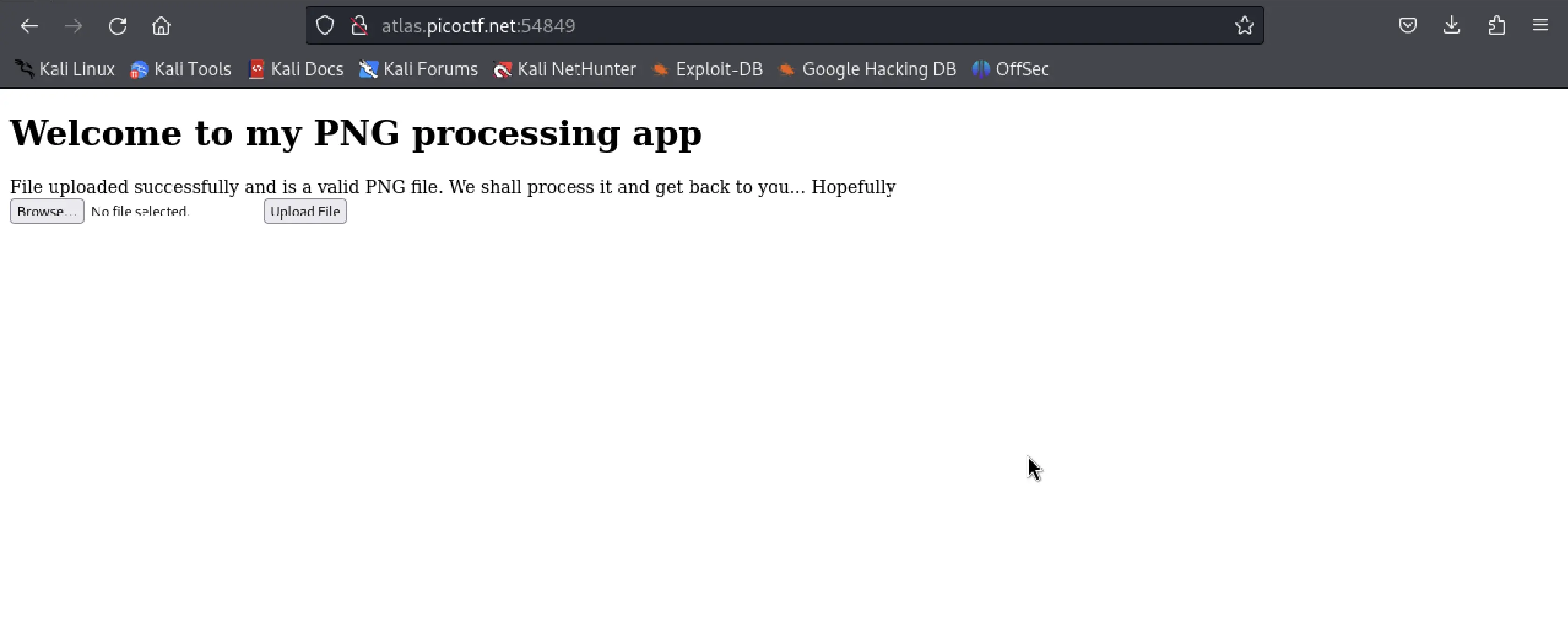
I uploaded a sample PNG image of 1MB to test it. The image was successfully uploaded and message on the site was changed to "==File uploaded successfully and is a valid PNG file. We shall process it and get back to you... Hopefully=="
and when tried to upload other file except .png extension it showed that it wasn't a valid PNG file. Despite also checking the source code, i found nothing. So, I moved to the next steps.
To gather more information, I used the host command to determine the website's IP address and followed up with an nmap.
host atlas.picoctf.net
Found the ip address. I ran nmap to identify open ports and services.
nmap -A -p 54849 -T4 {ip}
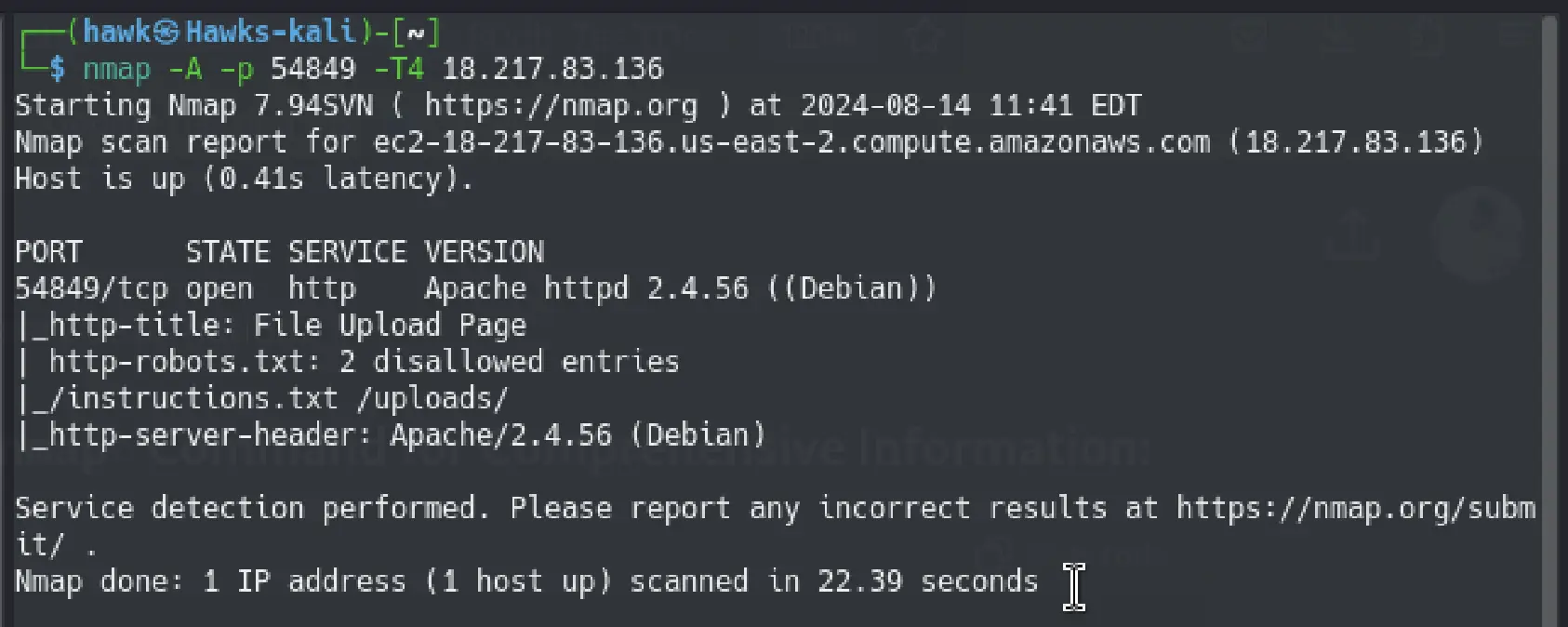
As you can see, I found 2 text files and a directory running on the port.
Instantly I looked into /robots.txt and found as following. The information are similar to what the nmap result said.