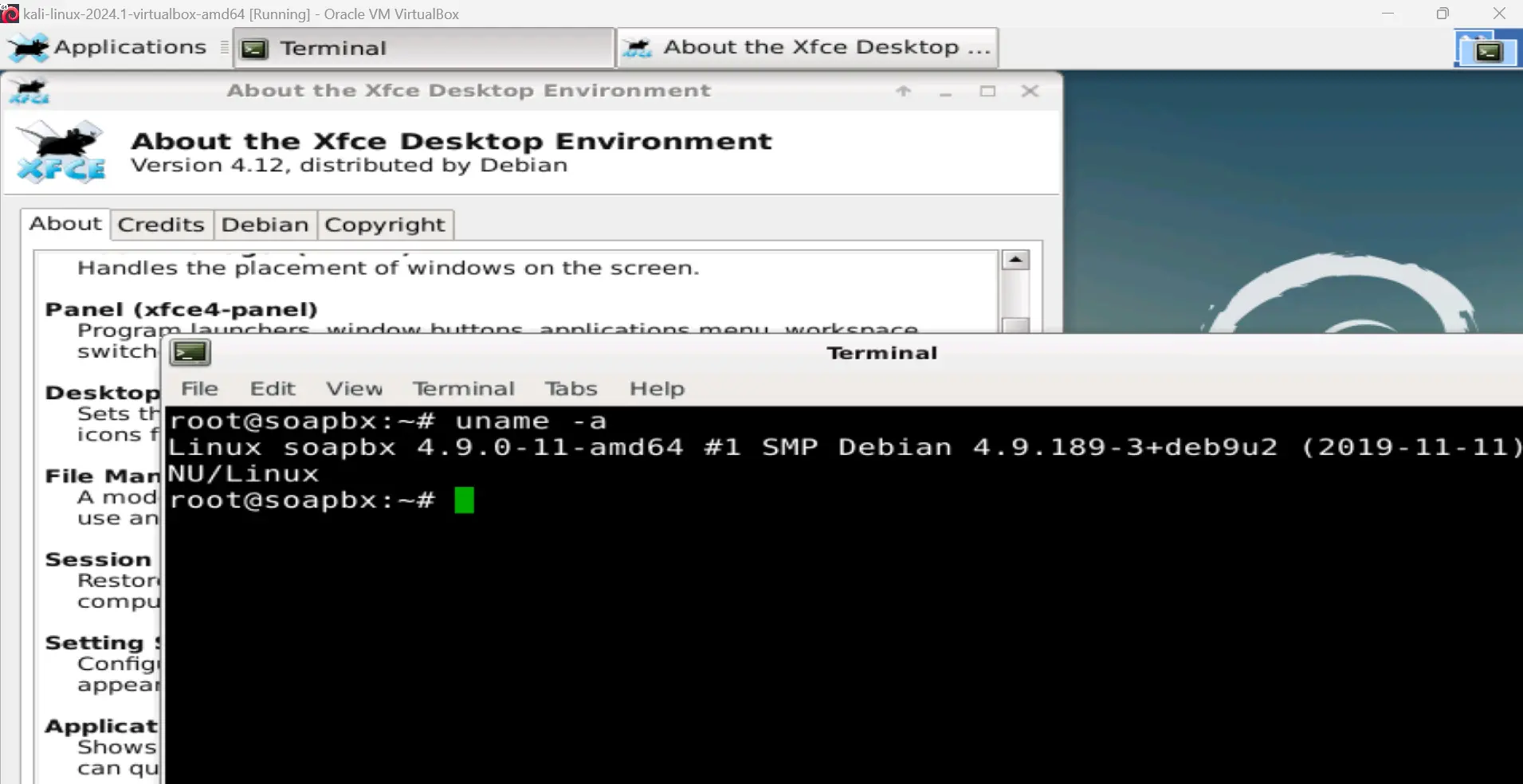
Hunting on Endpoints: Insights from OffSec TH-200 Course module 5 Section 1
In today’s world, our workstations, servers, and mobile devices are more vulnerable than ever. They are prime targets for cybercriminals looking to execute malicious code and infiltrate networks. With