OffSec - BackupBuddy

Backupbuddy is an intermediate-level challenge from the OffSec Playground, perfect for those aiming for their OSCP. It’s designed to test your enumeration skills, particularly web enumeration, to uncover vulnerabilities. The lab includes exploiting local file inclusion and leveraging crontabs for unauthorized access. The main goal is to understand and exploit these vulnerabilities to build stronger security awareness.
In this walkthrough, I’ll guide you through the process of compromising BackupBuddy, hosted on the OffSec Proving Grounds. The journey begins with a simple PHP file manager that used default credentials. The site was vulnerable to a directory traversal attack, which exposed an SSH key and granted a user shell. From there, a vulnerable SUID binary revealed a shared library misconfiguration, ultimately leading to a root shell. Let’s dive in!
To get started, I’ll run my go-to nmap scan to enumerate services and versions on all ports quickly. I’ll also save the scan results for easy reference later.
nmap -sC -sV -p- --min-rate 10000 [LAB_IP]
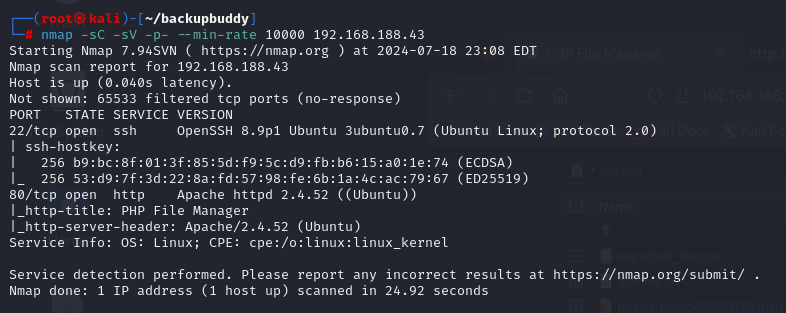
From the output, it’s clear this is an Ubuntu Linux machine with SSH running on port 22 and an Apache web server on port 80. The logical starting point is to take a closer look at the web server.
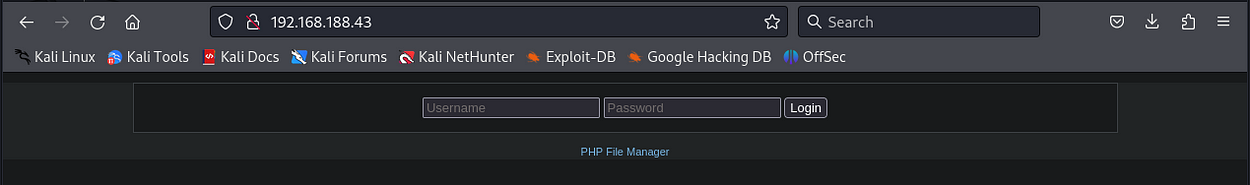
It’s a really simple login page with a link to PHP File Manager. Clicking on the link redirects you to the Github hosting the source code. This appears to be the core of Tiny PHP file manager.
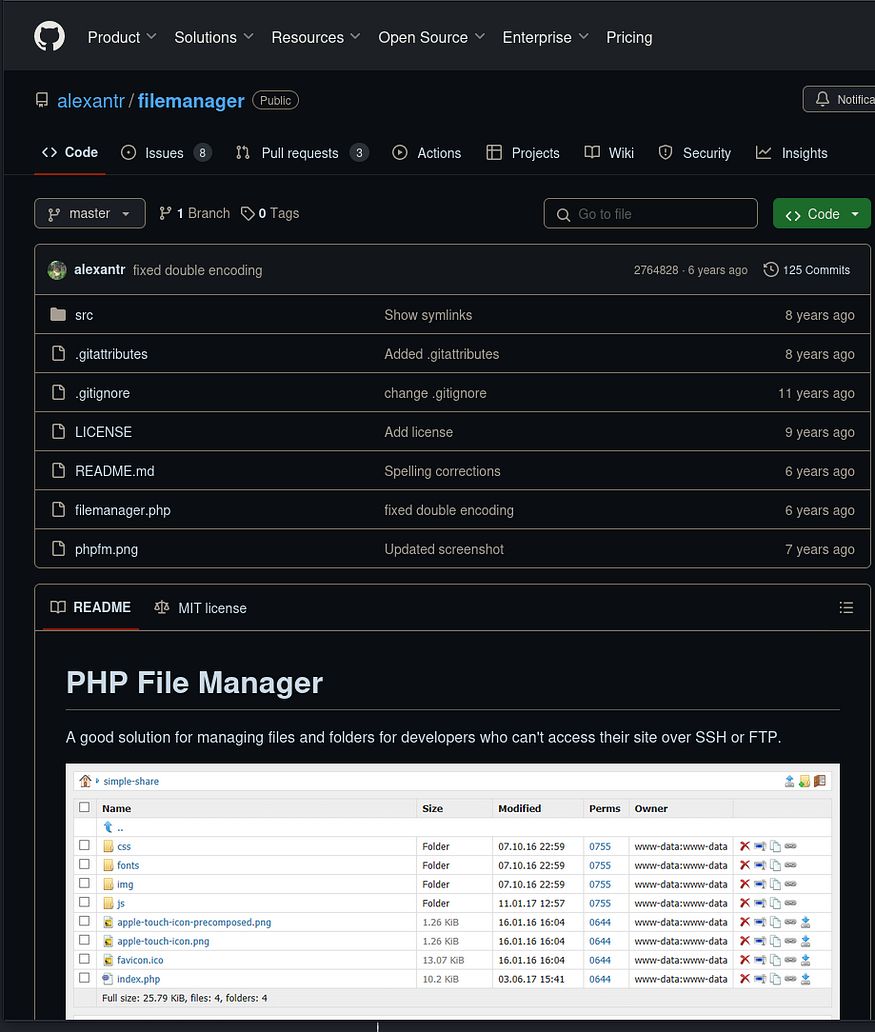
The first thing that stands out is how outdated the code is, which might work to my advantage. I checked the Issues and Security tabs on the GitHub repository, hoping to find some low-hanging fruit, but unfortunately, nothing of interest turned up.

