HTB Sky Recon - Hardware Challenge - Global Cyber Skills Benchmark CTF 2025 - Operation Blackout

CTF Writeup: Sky Recon - Hijacking a MAVLink Drone
Hey everyone! Today I'm going to walk you through the "Sky Recon" hardware challenge from Hack the Box Global Cyber Skills Benchmark CTF 2025 - Operation Blackout. This was a fun one that involved exploiting the MAVLink protocol to hijack a surveillance drone.
Challenge Description:
The scenario: Volnayan operatives have deployed a surveillance drone using the MAVLink protocol over our territory. It's transmitting intel. Our mission is to intercept the signal, seize control, and redirect the drone to a secure landing zone. The flag is in HTB{} format.
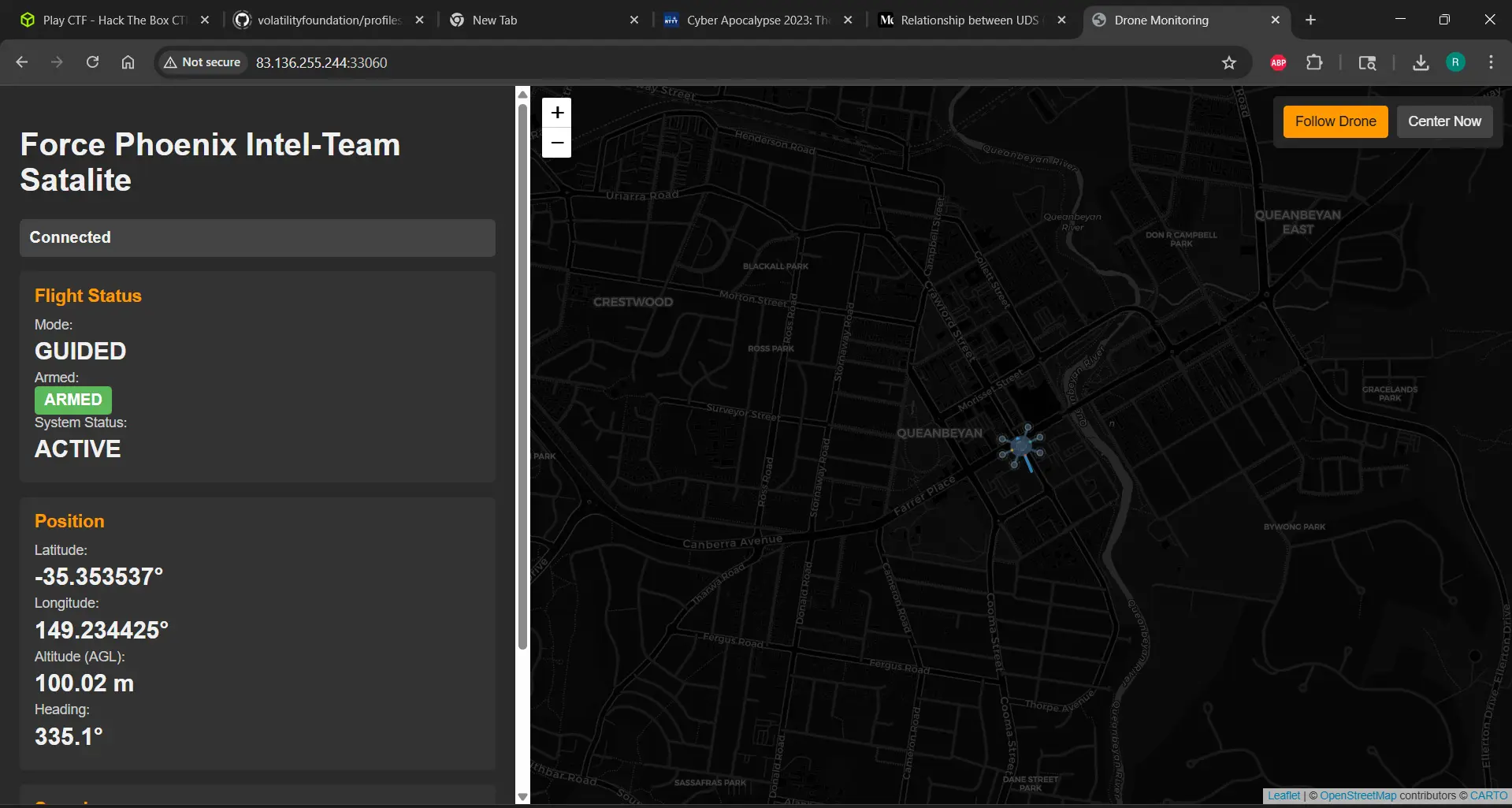
We were given two endpoints: 83.136.255.244:54988 and 83.136.255.244:33060, and a mission.pdf file.
Initial Reconnaissance
My first step was to look at the provided file and try to understand the environment.
We had mission.pdf.
Knowing the target protocol was MAVLink, I did some quick research.
web-search: "MAVLink protocol drone communication intercept exploit"
The search results confirmed that MAVLink, especially over radio or unencrypted TCP, can be vulnerable to injection attacks where an attacker can send commands to take control, disable failsafes, or redirect the drone if the communication isn't properly authenticated or encrypted. This aligned perfectly with the challenge description.
Identifying the Endpoints
We were given two endpoints: 83.136.255.244:54988 and 83.136.255.244:33060. Based on the challenge description and common MAVLink setups, one was the MAVLink telemetry/command stream, and the other was a web interface for monitoring or control.
We found that pymavlink is the standard library for MAVLink interaction in Python, I decided to use that.
Connecting to the Drone with Pymavlink
I installed pymavlink:
$ pip install pymavlink
Then, I wrote a small Python script to try connecting to the endpoints using pymavlink and wait for a heartbeat, which indicates a successful MAVLink connection.
# This was part of the initial drone_hijack.py script
import time
from pymavlink import mavutil
# Challenge endpoints
ENDPOINTS = [
('83.136.255.244', 54988),
('83.136.255.244', 33060)
]
def connect_to_drone():
"""Try to connect to the drone via MAVLink"""
print("[*] Attempting to connect to drone...")
for host, port in ENDPOINTS:
try:
print(f"[*] Trying {host}:{port}")
connection_string = f"tcp:{host}:{port}"
master = mavutil.mavlink_connection(connection_string)
print("[*] Waiting for heartbeat...")
master.wait_heartbeat(timeout=5)
print(f"[+] Connected to drone at {host}:{port}")
print(f"[+] System ID: {master.target_system}, Component ID: {master.target_component}")
return master
except Exception as e:
print(f"[-] Failed to connect to {host}:{port}: {e}")
continue
return None
# ... (rest of the script for hijacking)
Port 54988 was the MAVLink endpoint, and we successfully received a heartbeat. Port 33060 was the website.
MAVLink Hijacking Strategy
With a successful MAVLink connection, the goal was to take control and send the drone to the target coordinates: -35.36276, 149.16571. The common steps for a MAVLink takeover, especially when authentication is weak or absent, involve:
- Disabling the original Ground Control Station (GCS): Stop the drone from sending telemetry to the enemy's controller.
- Requesting control: Signal to the drone that our system is the new controller.
- Changing flight mode: Switch to a mode like
GUIDEDwhere we can send specific position commands. - Disabling failsafes: Prevent the drone from automatically returning home or landing if it loses connection to the original GCS.
- Sending target waypoints/positions: Command the drone to go to the secure landing zone.
- Maintaining control: Continuously send commands or monitor its progress.
Implementing the Hijacking Script (drone_hijack.py)
I incorporated the connection logic into a full hijacking script. The script performs the steps outlined above using pymavlink messages.
Here's the complete drone_hijack.py script: