Hack The Box - HTB - Fluffy


🤨 Enumeration :-
# Nmap 7.94SVN scan initiated as: /usr/lib/nmap/nmap -sCV -T4 --min-rate 10000 -p- -v -oA nmap/tcp_default [MACHINE_IP]
Nmap scan report for fluffy.htb ([MACHINE_IP])
Host is up (1.4s latency).
Not shown: 65523 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain?
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: fluffy.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-05-25T02:09:15+00:00; +1h31m29s from scanner time.
| ssl-cert: Subject: commonName=DC01.fluffy.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.fluffy.htb
| Issuer: commonName=fluffy-DC01-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-04-17T16:04:17
| Not valid after: 2026-04-17T16:04:17
| MD5: 2765:a68f:4883:dc6d:0969:5d0d:3666:c880
|_SHA-1: 72f3:1d5f:e6f3:b8ab:6b0e:dd77:5414:0d0c:abfe:e681
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: fluffy.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-05-25T02:09:15+00:00; +1h31m29s from scanner time.
| ssl-cert: Subject: commonName=DC01.fluffy.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, **DNS:DC01.fluffy.htb**
| Issuer: commonName=fluffy-DC01-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-04-17T16:04:17
| Not valid after: 2026-04-17T16:04:17
| MD5: 2765:a68f:4883:dc6d:0969:5d0d:3666:c880
|_SHA-1: 72f3:1d5f:e6f3:b8ab:6b0e:dd77:5414:0d0c:abfe:e681
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49678/tcp open msrpc Microsoft Windows RPC
49679/tcp open msrpc Microsoft Windows RPC
49683/tcp open msrpc Microsoft Windows RPC
49700/tcp open msrpc Microsoft Windows RPC
49741/tcp open msrpc Microsoft Windows RPC
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-05-25T02:08:33
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: 1h31m26s, deviation: 2s, median: 1h31m28s
cat /etc/hosts
[MACHINE_IP] DC01.fluffy.htb fluffy.htb DC01
cat /etc/krb5.conf
[libdefaults]
default_realm = FLUFFY.HTB
dns_lookup_realm = false
dns_lookup_kdc = false
ticket_lifetime = 24h
forwardable = true
udp_preference_limit = 1
default_tgs_enctypes = rc4-hmac
default_tkt_enctypes = rc4-hmac
permitted_enctypes = rc4-hmac
[realms]
FLUFFY.HTB = {
kdc = [MACHINE_IP]
admin_server = [MACHINE_IP]
}
[domain_realm]
.fluffy.htb = FLUFFY.HTB
fluffy.htb = FLUFFY.HTB
🔱 Initial Access :-
rusthound -d fluffy.htb -u 'j.fleischman' -p 'J0elTHEM4n1990!' -f fluffy.htb -n [MACHINE_IP] -z -o rusthound
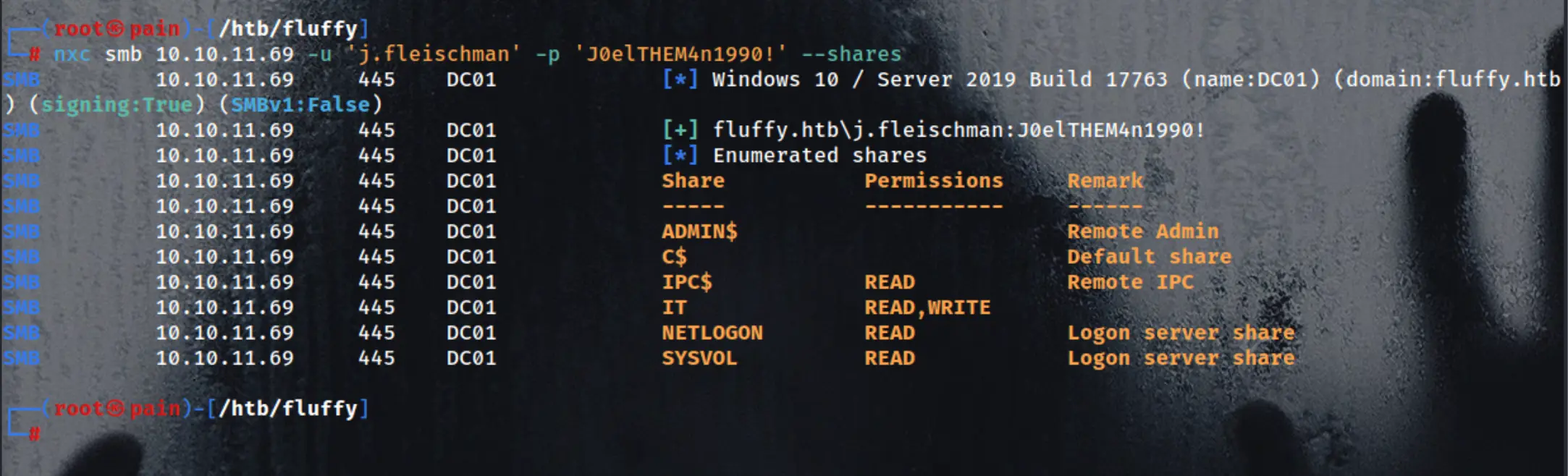
nxc smb [MACHINE_IP] -u 'j.fleischman' -p 'J0elTHEM4n1990!' --shares
smbclient \\\\[MACHINE_IP]\\IT -U 'j.fleischman%J0elTHEM4n1990!'
mget *
→ y
open Upgrade_Notice.pdf
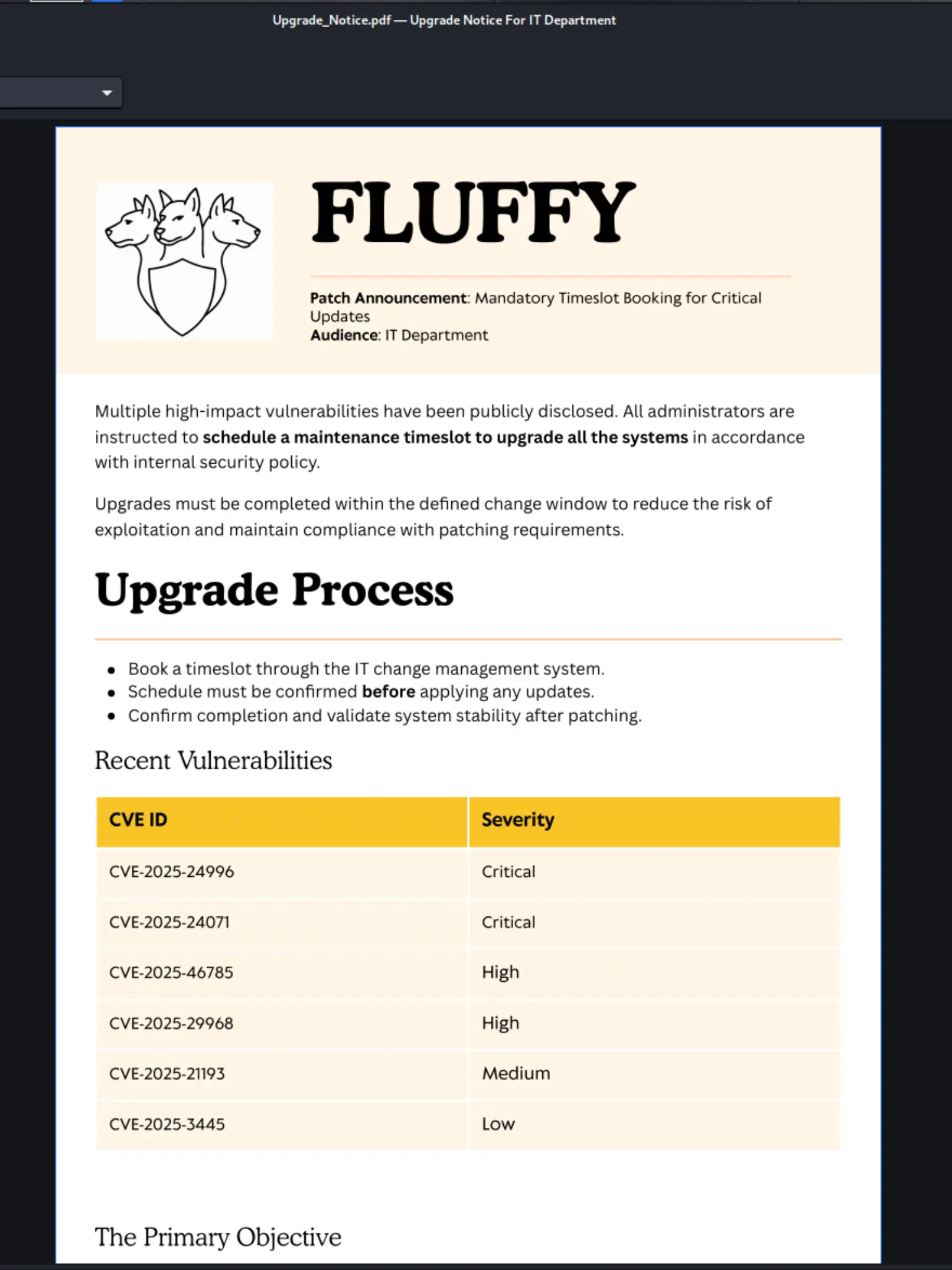
CVE-2025-24071
https://github.com/ThemeHackers/CVE-2025-24071.git
🔒 CVE-2025-24071 - Windows File Explorer Spoofing Vulnerability
📌 What is it?
A spoofing vulnerability in Windows File Explorer that can be exploited using specially crafted .library-ms files. It abuses the automatic file parsing and SMB trust behavior in Windows.