Hack The Box - HTB Artificial Writeup - Easy - Season 8 Weekly - June 21st, 2025

HackTheBox: Artificial - A Journey to Root
Overview
This post provides a comprehensive walkthrough of the 'Easy' HackTheBox machine "Artificial." We will dissect each phase of the attack, from initial reconnaissance to full system compromise. The attack path demonstrates a realistic chain of exploits, beginning with a sophisticated deserialization vulnerability in a web application, pivoting through the system by cracking user credentials, and culminating in privilege escalation by exploiting a misconfigured service.
- Machine: Artificial
- Operating System: Linux
- Difficulty: Easy
- Points: 20
- Key Vulnerabilities: Insecure Deserialization, Weak Hashing Algorithm (MD5), Credential Leakage, Command Injection.
MITRE ATT&CK® TTPs Employed
- Initial Access:
- T1190 - Exploit Public-Facing Application: Gaining initial entry by exploiting a vulnerability in the web application on port 80.
- Execution:
- T1059.006 - Command and Scripting Interpreter (Python): The target server executed our malicious Python code embedded within the uploaded TensorFlow model.
- T1059.004 - Command and Scripting Interpreter (Unix Shell): Used to obtain reverse shells via
bashand/bin/sh. - Credential Access:
- T1552.001 - Unsecured Credentials (Credentials in Files): Extracting password hashes from the
users.dbdatabase and theconfig.jsonconfiguration file. - T1110.001 - Brute Force (Password Cracking): Cracking the discovered MD5 and Bcrypt hashes offline with
hashcat. - Lateral Movement:
- T1021.004 - Remote Services (SSH): Using cracked credentials for the
gaeluser to log in and move from theappuser context. - Privilege Escalation:
- T1068 - Exploitation for Privilege Escalation: Abusing the misconfigured
Backrestservice, which was running as root, to execute commands. - Discovery:
- T1046 - Network Service Scanning: Using
nmapto identify open ports and services. - T1083 - File and Directory Discovery: Locating sensitive files like
users.dbandbackrest_backup.tar.gz. - Command and Control:
- T1105 - Ingress Tool Transfer: Uploading the malicious
exploit.h5file to the target server. - T1090 - Proxy: Using SSH local port forwarding to access a service bound to the target's localhost.
1. Initial Foothold: Web App to app User
1.1 Enumeration & Reconnaissance
Our process begins with a thorough nmap scan to map the target's attack surface.
Bash
# Scan all TCP ports, run default scripts (-sC), and enumerate service versions (-sV)
nmap -sC -sV -p- <TARGET_IP> -oN nmap_scan.txt
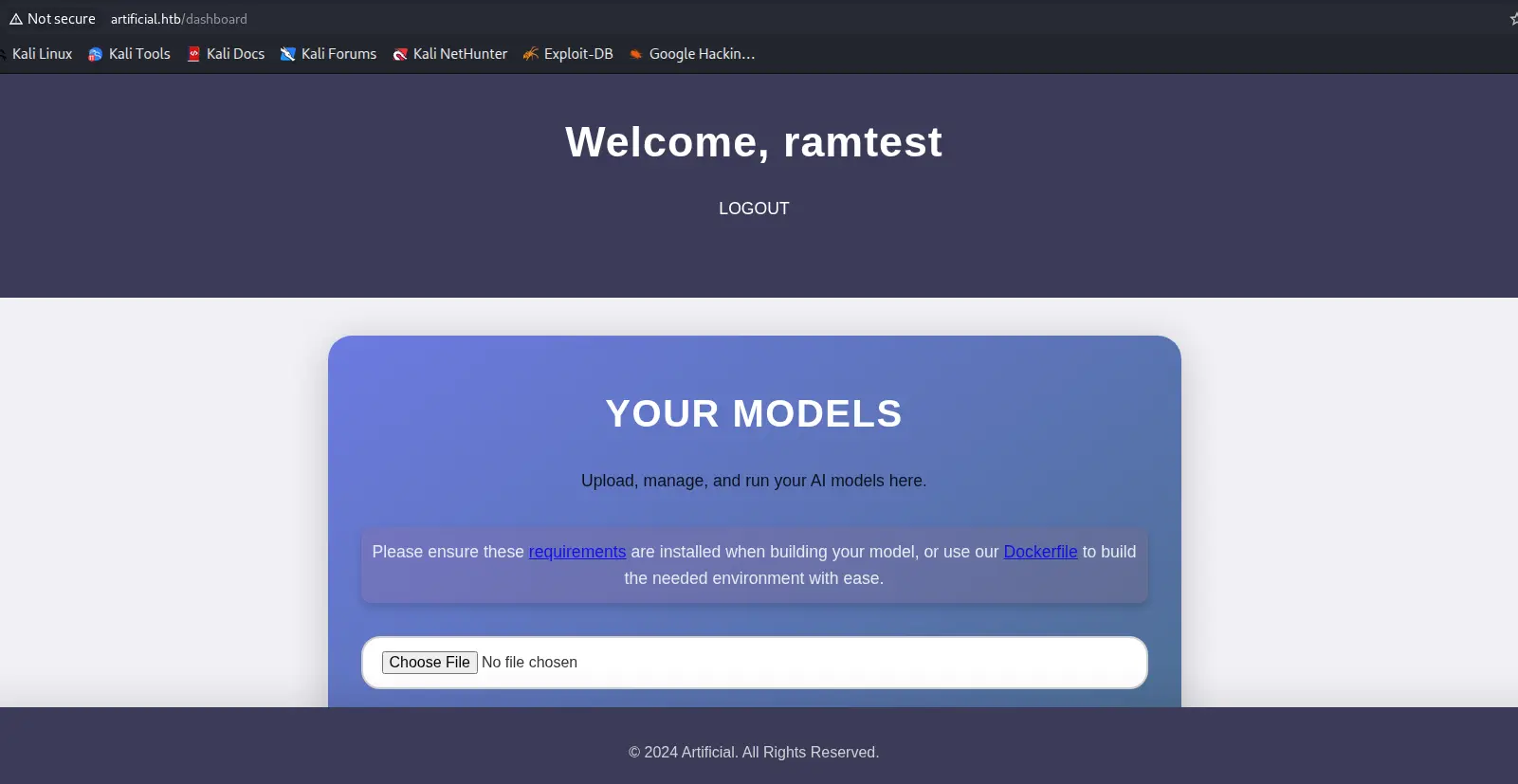
The scan reveals an OpenSSH server on port 22 and an Nginx web server on port 80. The website, "Artificial - AI Solutions," is a platform for uploading and running AI models. This type of functionality is a prime target for file upload and code execution vulnerabilities. Directory and Subdomain busting also came back empty. So we registered as a user and logged in.