Hack The Box Hardware Exploitation Track: Secure Digital
A deep dive into digital signals and embedded memory. In this challenge, we analyze a captured SPI communication stream between a microcontroller and a microSD card. What begins as a simple .sal file quickly unfolds into a forensic decoding of SPI transactions — isolating the moment a secret flag is transmitted. With nothing but waveforms, configuration tinkering, and Python at our disposal, we transform bits into bytes and bytes into a story.
The challenge description includes - "We accessed the embedded device's asynchronous serial debugging interface while it was operational and captured some messages that were being transmitted over it. Can you decode them?"

Challenge: Secure Digital Category: Hardware Exploitation Difficulty: Very Easy Points: 0 Link: Challenge Link
Initial Foothold
We began by downloading the provided archive: Secure Digital.zip. Inside was a familiar friend — a .sal file captured via the Saleae Logic Analyzer.
unzip "Secure Digital.zip"
The archive extracted a folder called secure_digital containing
trace_captured.sal.
You can checkout another similar challenge related to .sal file here.
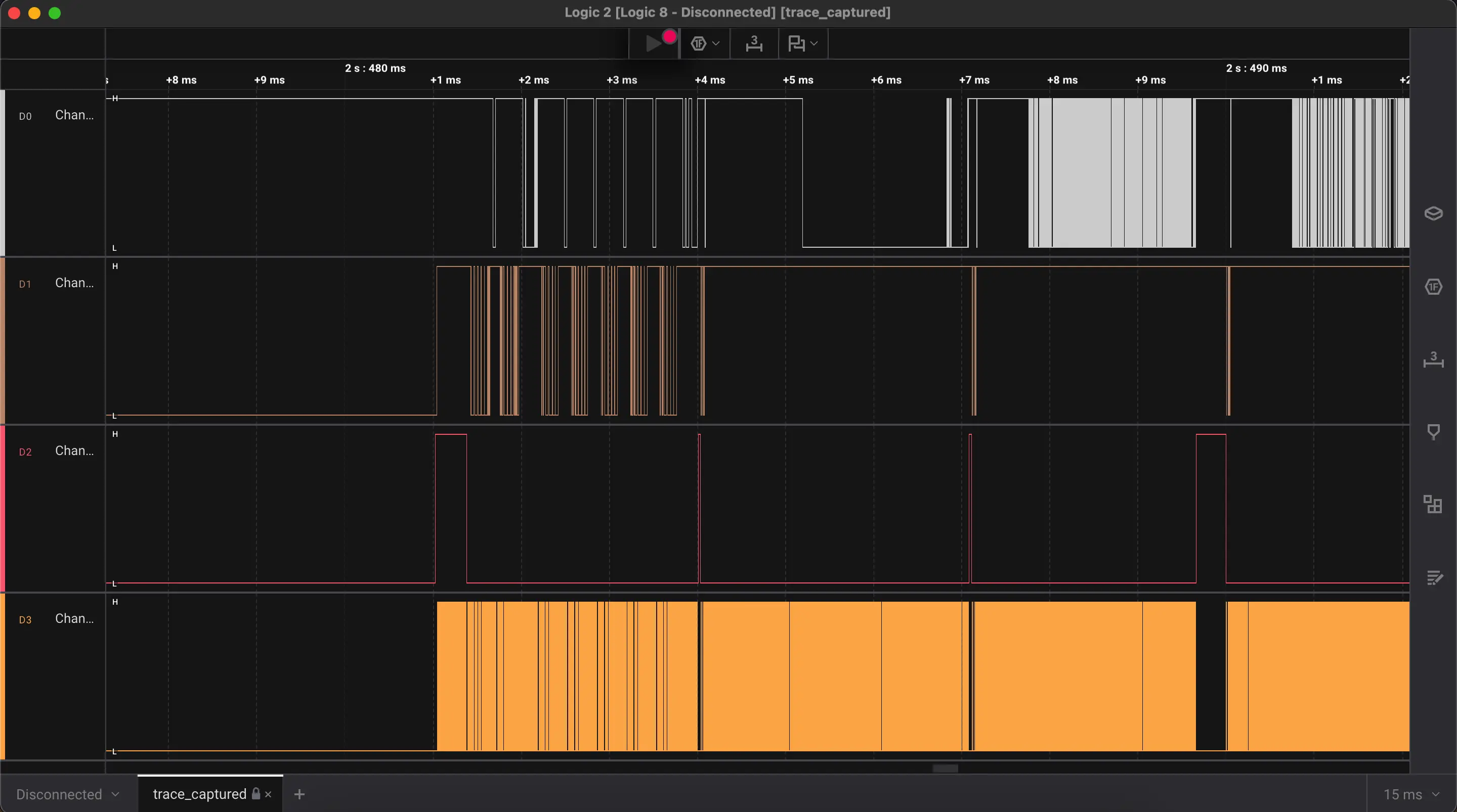
We fired up Logic 2, Saleae’s analysis software, and loaded it up.
Analyzing the Capture
Importing the file instantly populated waveform channels and metadata. But what protocol was used? We know from our research that microSD cards use Serial Peripheral Interface (SPI) as a communication protocol. While they are capable of operating in both SD (native) and SPI modes, SPI is commonly used in embedded systems where simplicity and fewer pin requirements are priorities. It’s a go-to for interfacing microcontrollers with SD cards.