Defcon 32 Hackman CTF 2024 Packet Capture Track Write-ups

In this write-up, I will walk you through the steps I took to solve challenges in Defcon 32 Hackman CTF 2024. The CTF has 8 different challenges curated for network packet analysis.
Unraveling the Mysteries of Packet Analysis
Packet analysis is a fundamental skill in network security, allowing professionals to dissect network traffic, uncover hidden data, and expose potential security threats. This challenge put those skills to the test, requiring me to decode an encrypted message buried within network packets.
What is Defcon & Why Are These Challenges Important?
DEF CON isn't just a conference; it's a hacker's paradise—a gathering of the sharpest minds in cybersecurity, held annually in Las Vegas, Nevada. Since its inception in 1993, DEF CON has grown into the ultimate battleground for security researchers, ethical hackers, and digital outlaws who push the limits of technology. Attendees range from security pros and students to federal agents, all converging in an electrifying atmosphere of talks, workshops, and mind-bending challenges. Among its legendary contests, Capture the Flag (CTF) stands as the ultimate test of hacking prowess, where teams battle in high-stakes digital warfare to breach and defend systems. With lockpicking, social engineering, and even beer-cooling competitions, DEF CON is more than just a conference—it’s an experience that defines hacker culture.
The challenges simulate real-world scenarios, sharpening investigative and analytical skills essential for professionals in the field.
Why This Write-Up Matters
This guide aims to document the approach to solving packet analysis challenges. By leveraging the right tools and methodologies, I solved all the challenges.
Challenge 1: Welcome To Packet Analysis
This challenge is really straight forward. Clicking on the description of the link the link takes me to this site. Clicking on the google map link one can find the first flag to start the track with.
Challenge 2: Baby shark doo doo..
Challenge 2 Breakdown & Step-by-Step Solution
Step 1: Dissecting the Packet Capture
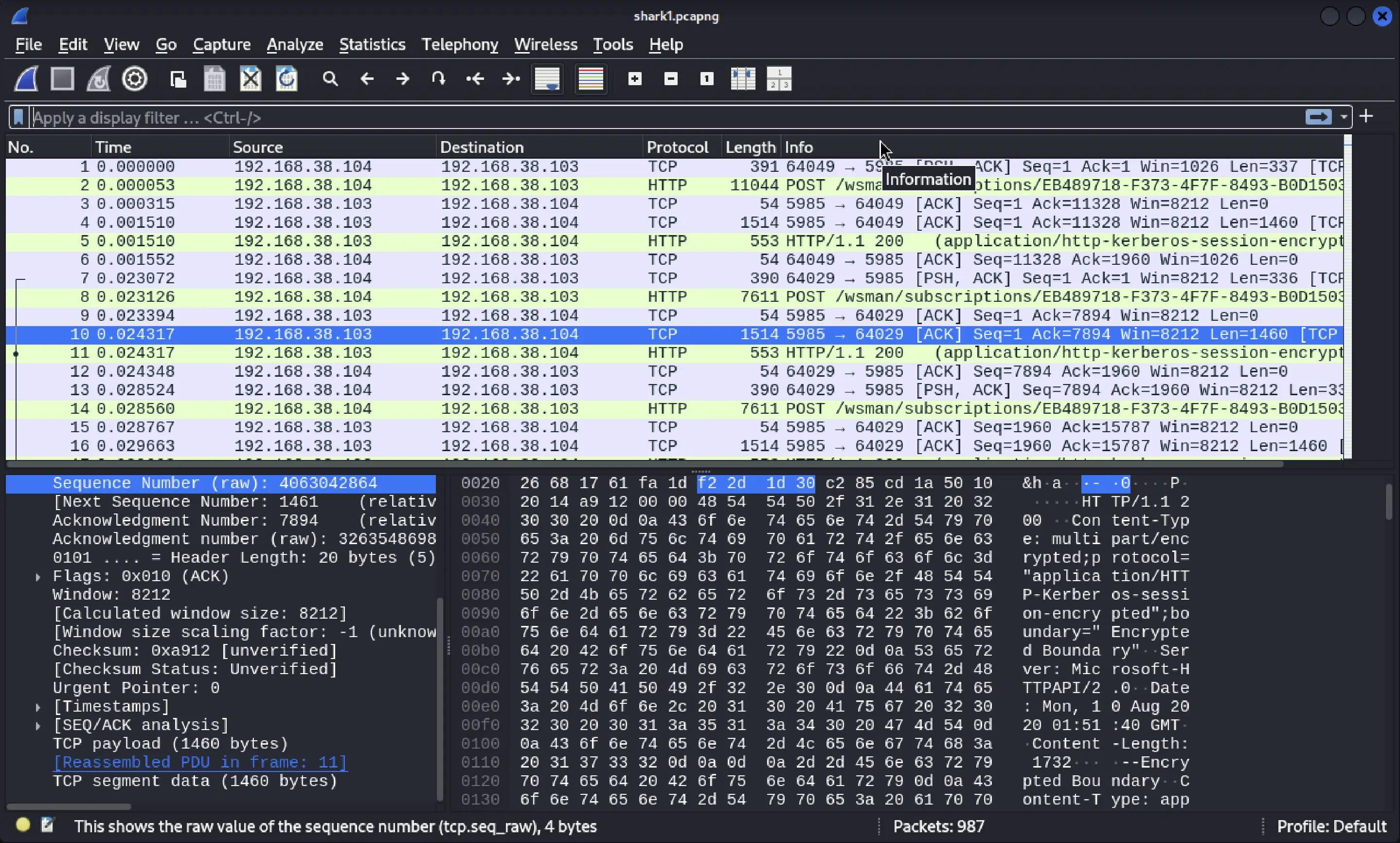
The challenge provided a file, shark1.pcapng, containing captured network traffic. I opened it in Wireshark, a powerful tool for analyzing network communications.
Key Findings:
Applying the filter tcp.stream eq 5 isolated the relevant TCP conversation.
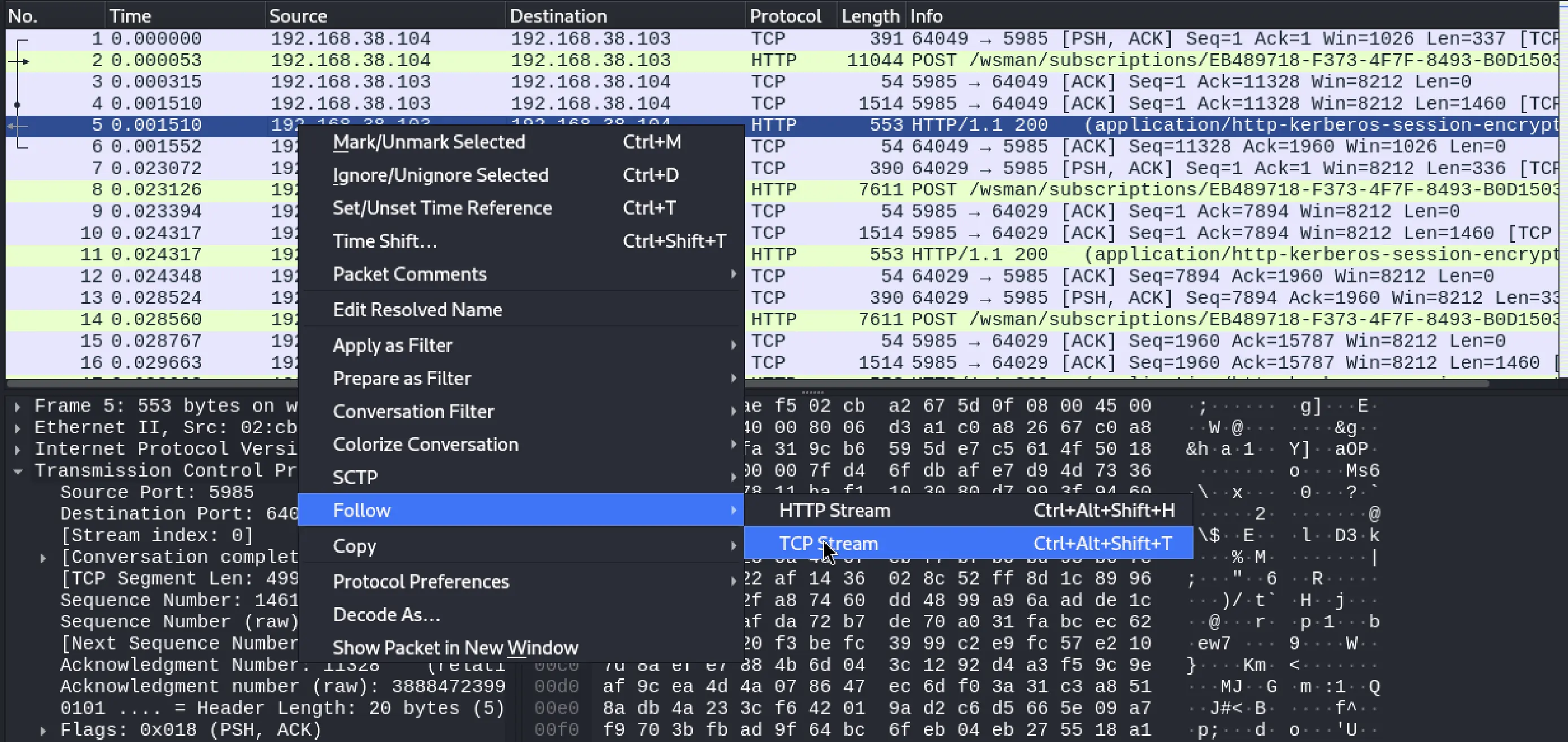
This conversation contained HTTP traffic, which, upon deeper inspection, revealed a suspiciously encoded text string.
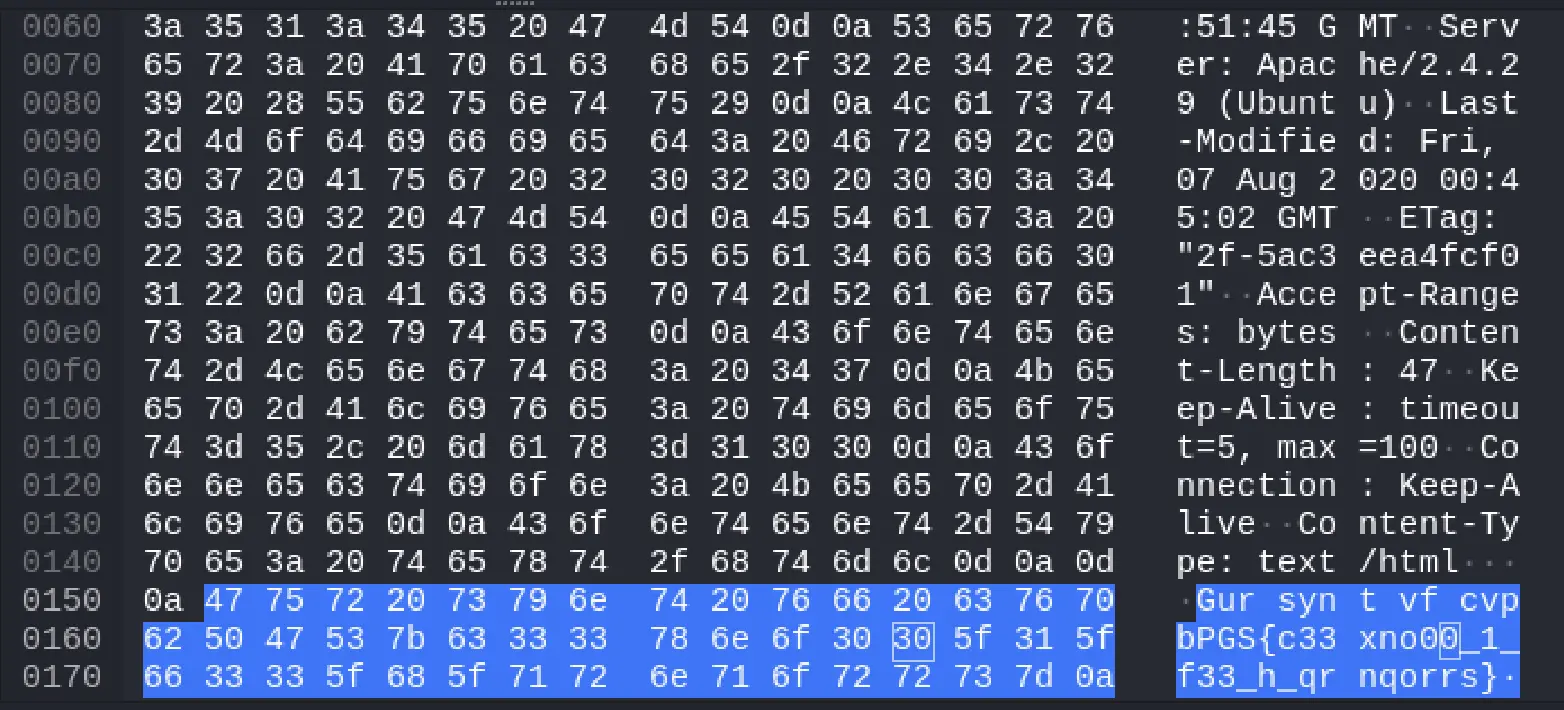
Extracted encoded message:
Gur synt vf cvpbPGS{c33xno00_1_f33_h_qrnqorrs}
This string was an immediate hint that it had undergone some form of obfuscation.
Step 2: Cracking the Cipher
To determine the encryption method, I used quipqiup, an online cryptogram solver. It identified the message as being encoded with ROT13, a simple substitution cipher where each letter is shifted forward by 13 places in the alphabet.

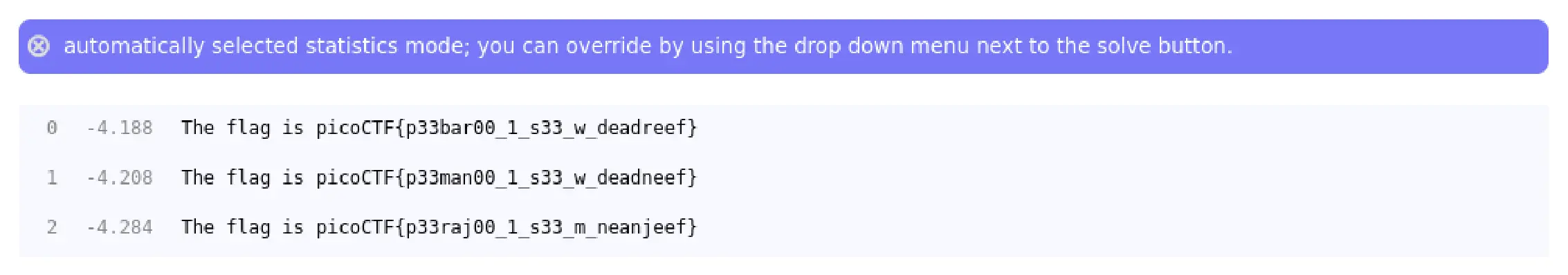
Why ROT13?
ROT13 is a basic but effective encoding technique often used to obscure text in CTF challenges. Since it's a symmetric cipher, applying ROT13 again reverses the transformation, revealing the original message.