Dawn

Nov 13 2023
Target:
[LAB_IP]
Prep
General Mind Map: https://xmind.app/m/QsNUEz/
Confirm docker is installed and set rustscan as an alias or add to bashrc / fish config due to it being able to scan all ports and services in 10 seconds
alias rustscan='sudo docker run -it --rm --name rustscan rustscan/rustscan:2.1.1 -a'
Create directory for target and enter it
mkdir ClamAV
cd ClamAV
Prep a nc listener
nc -nlvp 4444
Confirm ip address
hostname -I
My IP
[LAB_IP]
Prep Rev Shells https://revshells.com
Recon
Start with a quick open port scan
rustscan [LAB_IP]
PORT STATE SERVICE REASON 80/tcp open http syn-ack 139/tcp open netbios-ssn syn-ack 445/tcp open microsoft-ds syn-ack 3306/tcp open mysql syn-ack
Quick OS check
sudo nmap -O --top-ports 1000 -v -T4 [LAB_IP] -oN osType.nmap
No exact OS matches for host
Follow up with a service scan on those open ports
sudo nmap -sC -sV -p80,139,445,3306 -v -T5 [LAB_IP] -oN services.nmap
PORT STATE SERVICE VERSION
Port 80/tcp open http Apache httpd 2.4.38 ((Debian))
|http-title: Site doesn't have a title (text/html). | http-methods: | Supported Methods: OPTIONS HEAD GET POST |_http-server-header: Apache/2.4.38 (Debian)
sudo nmap -sV --script=http-title,http-enum,http-favicon,http-methods,http-passwd,http-robots.txt,http-sql-injection -p 80 -T5 [LAB_IP] -oN http.nmap
PORT STATE SERVICE VERSION 80/tcp open http Apache httpd 2.4.38 ((Debian)) |http-server-header: Apache/2.4.38 (Debian) |http-title: Site doesn't have a title (text/html). | http-methods: | Supported Methods: OPTIONS HEAD GET POST | http-enum: | /logs/: Logs
Kernel Exploits
searchsploit Apache 2.4.38
Apache 2.4.17 < 2.4.38 - 'apache2ctl graceful' 'logrotate' Local Privilege Escalation linux/local/46676.php
Target URL:
http://[LAB_IP]
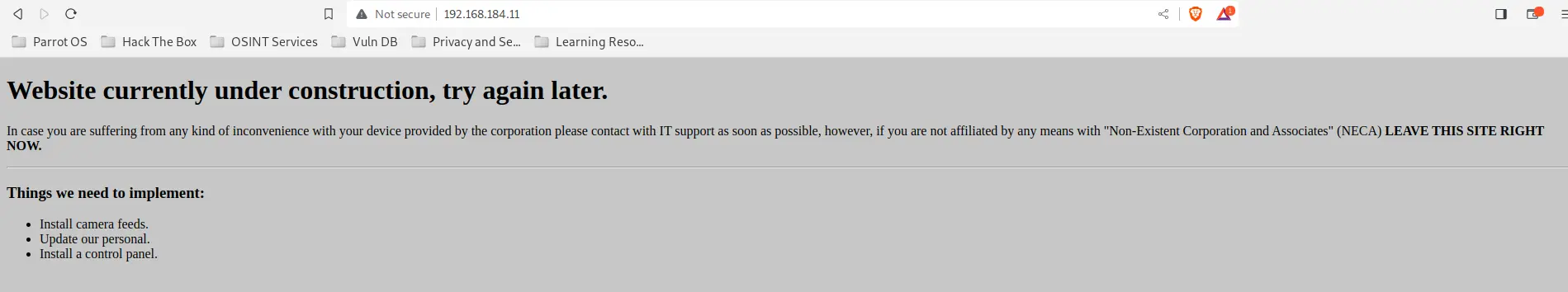 Website home page mentions CCTV
Website home page mentions CCTV
Check for non-navigable directories
dirbuster
- Run at
50threads - Wordlist location:
/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
Dir found: / - 200 Dir found: /icons/ - 403 Dir found: /icons/small/ - 403 Dir found: /logs/ - 200 File found: /logs/auth.log - 403 File found: /logs/daemon.log - 403 File found: /logs/error.log - 403 File found: /logs/management.log - 200 Dir found: /cctv/ - 403 Dir found: /server-status/ - 403
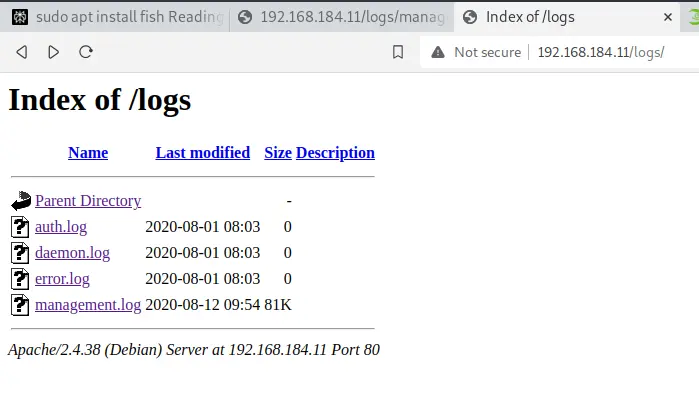 Log directory
Log directory
Management Logs are accessible. Also some interesting folders found
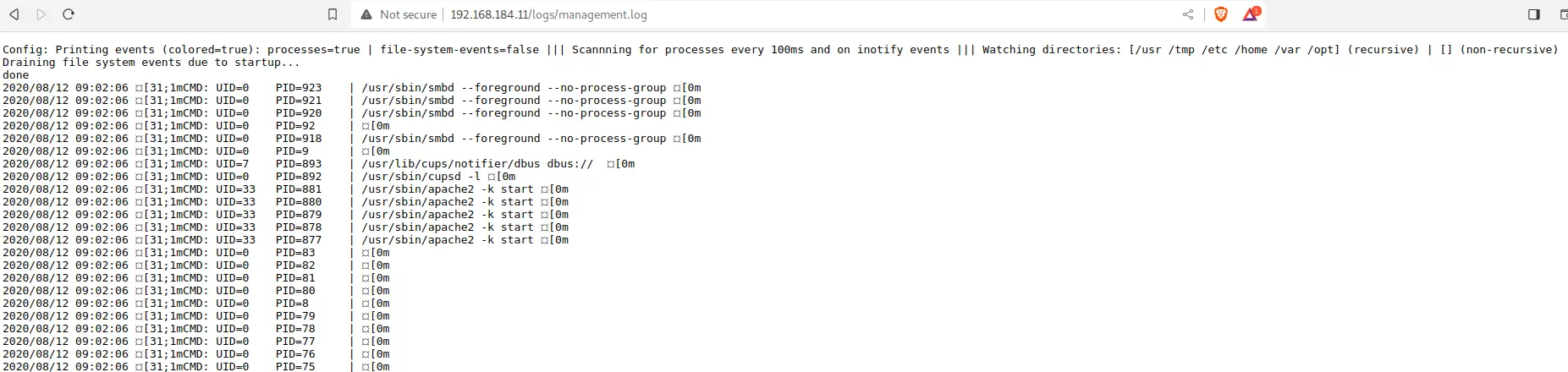 Looks like logs with printer jobs and cron edits
Too many logs so I will pull unique records from the command column
Looks like logs with printer jobs and cron edits
Too many logs so I will pull unique records from the command column
Sorting and removing duplicates from the log
cat logDump.txt | cut -d "|" -f2 | sort | uniq