picoCTF 2021 Solution - Wireshark doo dooo do doo...
Solving a CTF Challenge: Decoding the Secret Message In this blog post, I will walk you through the steps I took to solve a Capture the Flag (CTF) challenge, where
Solving a CTF Challenge: Decoding the Secret Message In this blog post, I will walk you through the steps I took to solve a Capture the Flag (CTF) challenge, where

Upon spawning the machine, we got the ip address of the target machine. Let's run nmap to find the open ports using the following command - nmap -sV

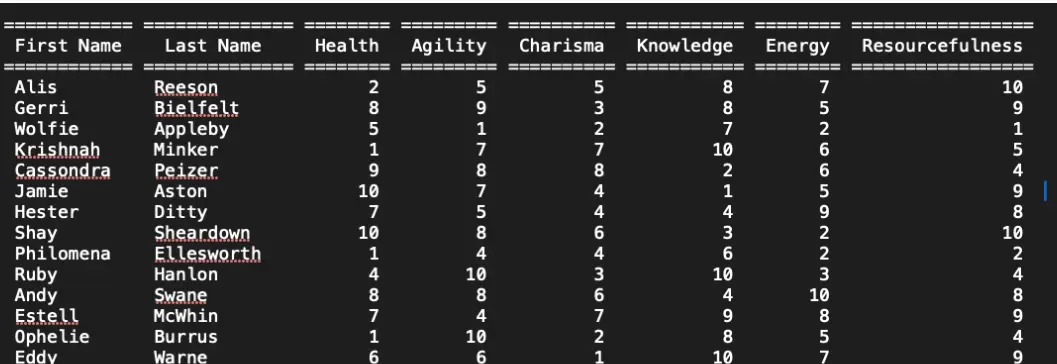
Hijacking the outpost responsible for housing the messengers of the core gangs, we have managed to intercept communications between a newly-elected leader and the Tariaki, a well-established and powerful gang.
Not too long ago, your cyborg detective friend John Love told you he heard some strange rumours from some folks in the Establishment that he's searching into. They
The crew sets their sights on an abandoned fertilizer plant, a desolate structure rumored to hold a cache of ammonium nitrate—crucial for their makeshift explosives. Navigating through the plant’
Security Incident Summary On April 19, 2024, between 4:35 PM and 6:00 PM, our network experienced a coordinated cyberattack involving multiple offenses. The incident began with over 109
Hello everyone! I am a entering into cybersecurity and just cracked my first challenge on the Hackthebox platform. Today, I'm sharing my experience tackling one of the "

Executive Summary Incident Overview On April 19, 2024, a security breach was detected in our AWS account, originating from a Russian IP address. The unauthorized access led to the deployment

Summary It checks out the system environment, sets up a scheduled service, downloads google chrome profile cache data, and uploads it to a remote server. A highly SEO optimized github

Demo Summary CVE-2024-1086 is a critical vulnerability in the Linux kernel that allows an attacker to gain full root privileges on a wide range of systems. This exploit, dubbed CVE-2024-1086

Summary CVE-2021-3493 is a #linux-kernel exploit that basically takes vulnerable default configs for Ubuntu Linux kernels up to version 5.10 (Patched in 5.11) and gives access to the

:::info Search Kali's Tools on their tool search engine: https://www.kali.org/tools/ ::: :::tip Run port 443 since it's never blocked on firewalls. :::

Target is [LAB_IP] connecting via openvpn openvpn oscp.vpn [ ](https://www.prestonzen.com/publications/cybersecurity/oscp/linux/sunset-noontide#h.9ds2jjg2j16) Recon nmap -sC -sV -p- -vv [LAB_IP] PORT

Enumerate Looking for targets on subnet. Found [LAB_IP] ##Nmap Adding -O for OS detection in the field sudo nmap -sT -sV -sC -O --open -p- [LAB_IP] -oN sumo.