Access

Summary
Given target is ip: [LAB_IP]
Challenge says it's a windows system
#Reconnaissance
#Nmap
sudo nmap -Pn -n -sC -sV -p- -v --open -oN all-ports.nmap [LAB_IP]
sudo - half open (faster scan) -Pn - Skip port scan -n - Skip DNS -sC - Default Scripts -sV - Service version -p- - all ports -v - verbose live output --open - only shows open ports
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Apache httpd 2.4.48 ((Win64) OpenSSL/1.1.1k PHP/8.0.7)
|_http-title: Access The Event
|_http-server-header: Apache/2.4.48 (Win64) OpenSSL/1.1.1k PHP/8.0.7
| http-methods:
| Supported Methods: GET POST OPTIONS HEAD TRACE
|_ Potentially risky methods: TRACE
|_http-favicon: Unknown favicon MD5: FED84E16B6CCFE88EE7FFAAE5DFEFD34
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-03-21 13:08:14Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: access.offsec0., Site: Default-First-Sit
e-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: access.offsec0., Site: Default-First-Sit
e-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49673/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49674/tcp open msrpc Microsoft Windows RPC
49677/tcp open msrpc Microsoft Windows RPC
49701/tcp open msrpc Microsoft Windows RPC
49782/tcp open msrpc Microsoft Windows RPC
Service Info: Host: SERVER; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2024-03-21T13:09:08
|_ start_date: N/A
#Web-Application-Reconnaissance
http website for an event about page: http://[LAB_IP]/

#Whatweb
whatweb http://[LAB_IP]/
http://[LAB_IP]/ [200 OK] Apache[2.4.48], Bootstrap, Country[RESERVED][ZZ], Email[info@example.com], Frame, HT ML5, HTTPServer[Apache/2.4.48 (Win64) OpenSSL/1.1.1k PHP/8.0.7], IP[[LAB_IP]], Lightbox, OpenSSL[1.1.1k], PHP[ 8.0.7], Script, Title[Access The Event]
#Nikto
nikto -h [LAB_IP]
- Serv`er: Apache/2.4.48 (Win64) OpenSSL/1.1.1k PHP/8.0.7
- /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTT P/Headers/X-Frame-Options
- /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missin g-content-type-header/
- Apache/2.4.48 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch .
- PHP/8.0.7 appears to be outdated (current is at least 8.1.5), PHP 7.4.28 for the 7.4 branch.
- OpenSSL/1.1.1k appears to be outdated (current is at least 3.0.7). OpenSSL 1.1.1s is current for the 1.x branch and w ill be supported until Nov 11 2023.
- OPTIONS: Allowed HTTP Methods: GET, POST, OPTIONS, HEAD, TRACE .
- /: HTTP TRACE method is active which suggests the host is vulnerable to XST. See: https://owasp.org/www-community/att acks/Cross_Site_Tracing
- /ticket.php?id=99999: Retrieved x-powered-by header: PHP/8.0.7.`
#Directory-Enumeration
#Dirbuster
dirbuster
- Run at
10threads - Wordlist location:
/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
Add in other file types:
php,sh,txt,html

#Gobuster
sudo gobuster dir -w '/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt'
-u http://[LAB_IP]:80 -t 21 -b 400,403,404
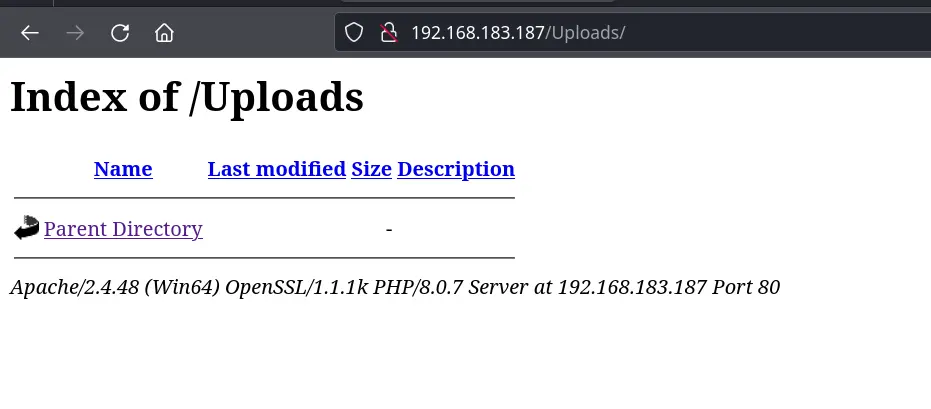
/uploads (Status: 301) [Size: 344] [--> http://[LAB_IP]/uploads/] /assets (Status: 301) [Size: 343] [--> http://[LAB_IP]/assets/] /forms (Status: 301) [Size: 342] [--> http://[LAB_IP]/forms/] /examples (Status: 503) [Size: 404] /Forms (Status: 301) [Size: 342] [--> http://[LAB_IP]/Forms/] /Assets (Status: 301) [Size: 343] [--> http://[LAB_IP]/Assets/] /Uploads (Status: 301) [Size: 344] [--> http://[LAB_IP]/Uploads/]
Gobuster seems faster to implement and is much easier to copy & paste
Uploads hints there may be directory navigation possible
#DotDotPwn
dotdotpwn -o windows -h [LAB_IP] -m http
add -q to not print every attempt and keep the screen clean
#Version-Vulnerability-Scanning
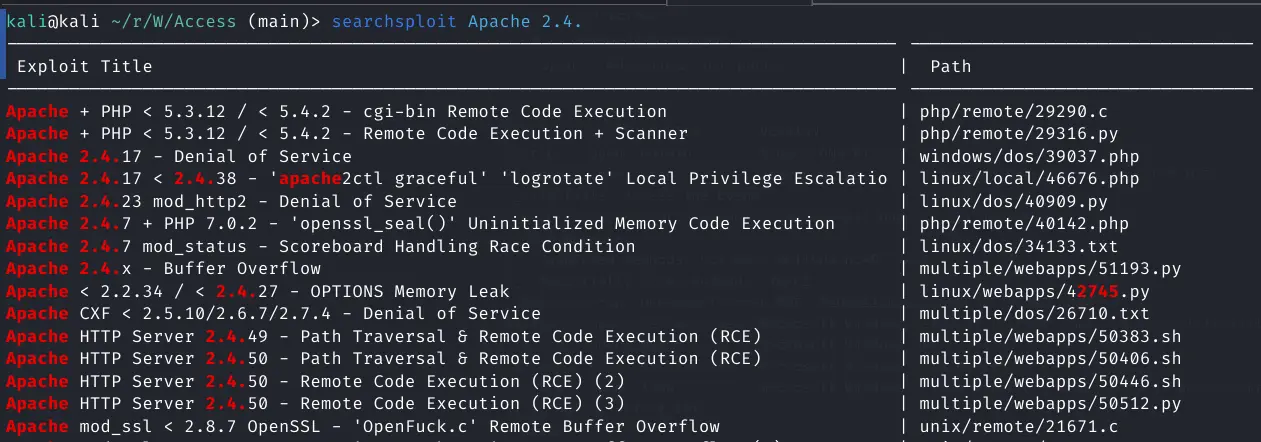
searchsploit Apache 2.4
Nothing of note speicifically for 2.4.48
#Web-Application-Enumeration
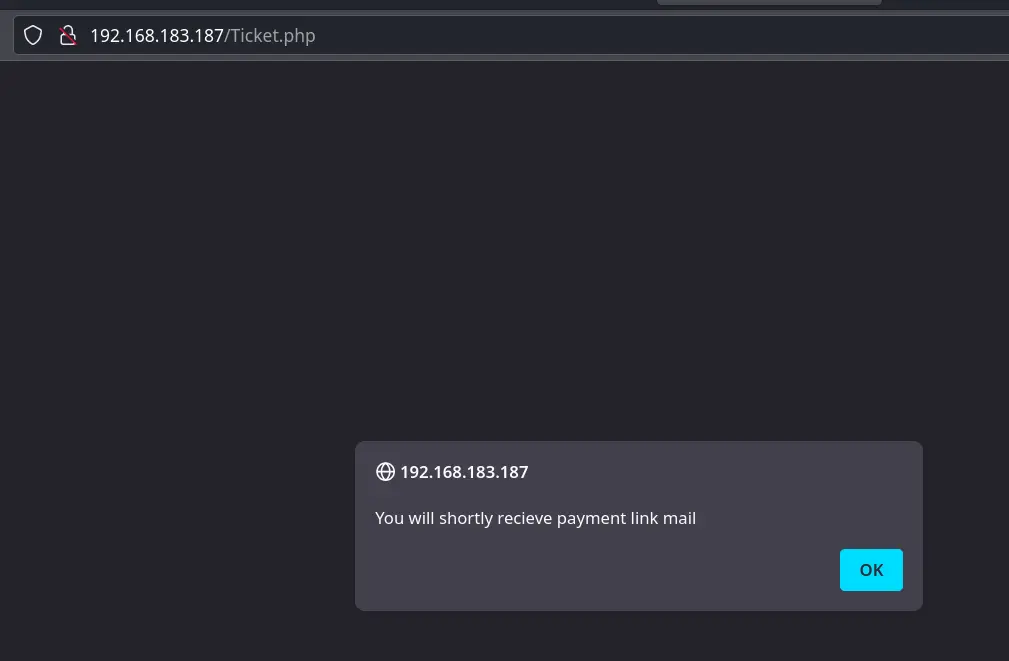
Found a file uploader form field
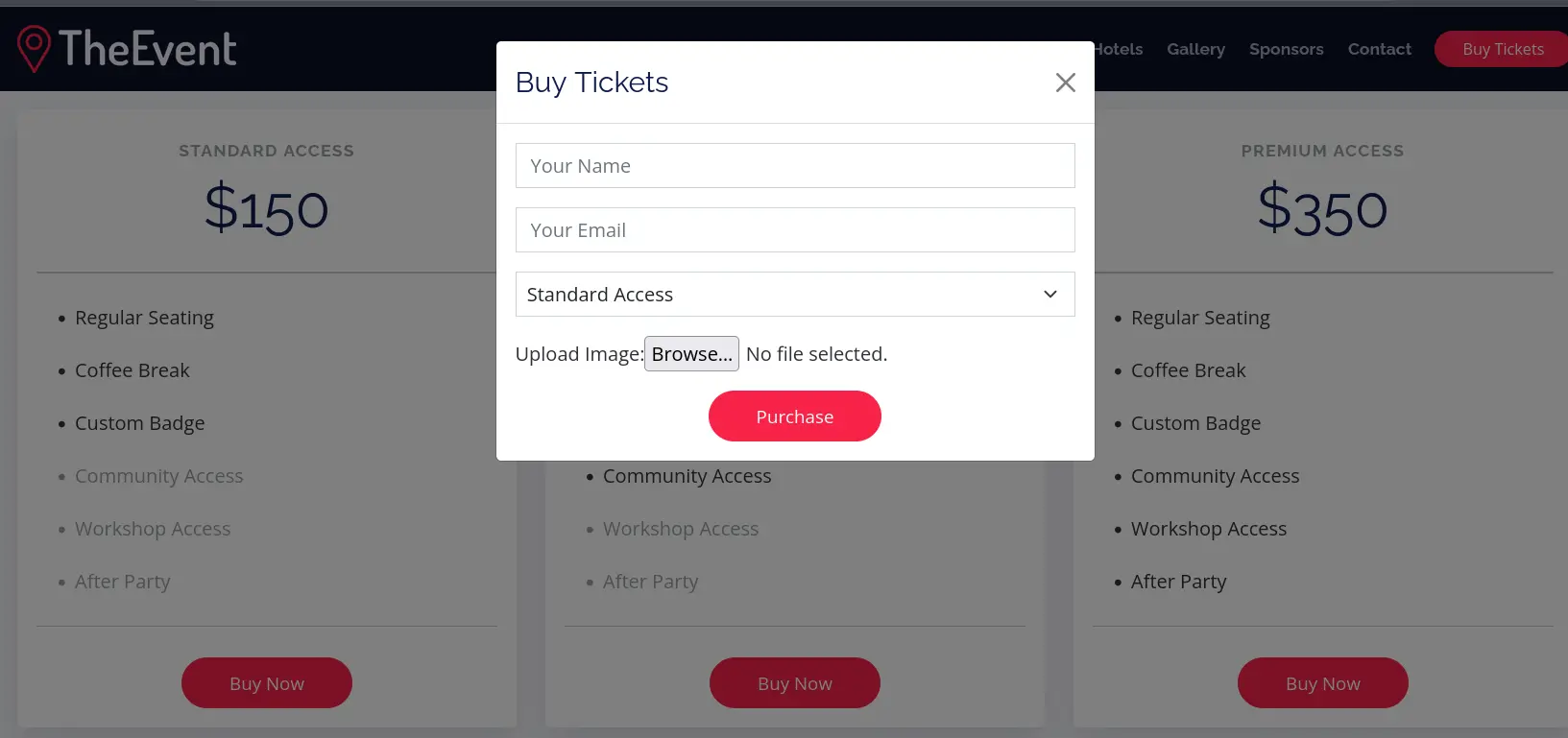
In case they have a real email server hooked that's vulnerable, I'll give them an email at: https://www.guerrillamail.com/
Seems there isn't an active email server attached

Will try to send a payload via the upload file form field